Apple pulls popular Instagram client 'InstaAgent' from iOS App Store after malware discovery
Last updated
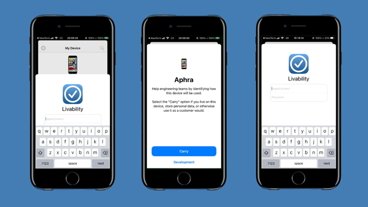
A popular Instagram profile analyzer was on Tuesday pulled from the iOS App Store after being outed as malware by a German developer who found the app harvesting usernames and passwords.
According to a Peppersoft developer who goes by the Twitter handle David L-R, "Who Viewed Your Profile — InstaAgent" was a nefarious username and password harvesting tool masquerading as an app for monitoring Instagram profile visitors.
Digging into the app's code revealed sensitive account information being sent unencrypted to a remote server, instagram.zunamedia.com, and in some cases used to log in and post unauthorized photos to users' Instagram feeds. David L-R notes the remote server is not connected to Instagram's official network.
Before being yanked from the App Store, InstaAgent was a chart-topping free app in multiple countries including Canada and the UK, suggesting thousands of unsuspecting users unwittingly handed over their Instagram credentials. Hard numbers are currently unavailable, but the developer guesses as many as 500,000 users downloaded the app. The metric matches up with InstaAgent's performance on the Google Play app store, which removed the title earlier today.
While no longer available, the iOS App Store still contains Instagram profile analytics apps looking to capitalize on InstaAgent's success. Some offerings share similar titles like "Who Viewed My Profile" and "Who Viewed My Instagram Profile," while many sport icons showing a shadowy figure wearing a fedora. Instagram urges customers not download, log in or interact with third-party apps.
Making it past Apple's review process is cause for concern, but that InstaAgent remained unscrutinized as a high profile app — a top performer in some App Store regions — for so long is perhaps more troubling.
Apple's last dealt with a major App Store malware penetration in September when Chinese developers unknowingly used modified versions of Xcode to write and upload apps. Dubbed XcodeGhost, the rogue development program infected legitimate apps to mine user data. Apple ultimately wiped the store clean and began hosting official Xcode copies on Chinese servers to speed up download time, the main reason developers in the country had turned to unsanctioned software versions.
 AppleInsider Staff
AppleInsider Staff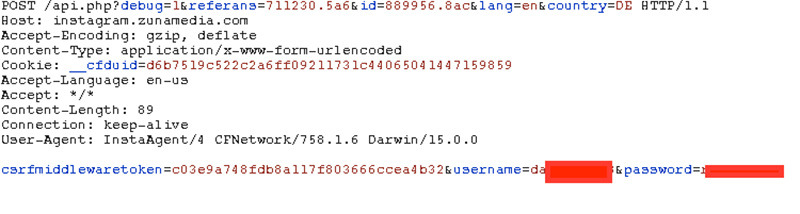













 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly

 William Gallagher
William Gallagher
 Malcolm Owen
Malcolm Owen
 Christine McKee
Christine McKee










20 Comments
It's time Apple gets serious about this, this is happening far too often for anyone to be comfortable. Claims about caring about user data privacy are undermined by incompetent verification of apps in the Store.
This is a good opportunity for the usual suspects to post FUD. You know who you are.
looks like if governments want a backdoor they need only make an app, sheesh.
[quote name="TheWhiteFalcon" url="/t/190058/apple-pulls-popular-instagram-client-instaagent-from-ios-app-store-after-malware-discovery#post_2804331"]It's time Apple gets serious about this, this is happening far too often for anyone to be comfortable. Claims about caring about user data privacy are undermined by incompetent verification of apps in the Store.[/quote] What a load of crap. This is not Apple's fault. There are lots of Apps that work as third party clients to access other services (think of e-mail programs where you need to provide your e-mail and password before they can access your account). It would be trivial for a developer of an e-mail App to store your credentials and later on send them to another server. Or, use your e-mail account to send themselves an e-mail with your information. How do you suggest Apple check for this?
[quote name="revenant" url="/t/190058/apple-pulls-popular-instagram-client-instaagent-from-ios-app-store-after-malware-discovery#post_2804342"]looks like if governments want a backdoor they need only make an app, sheesh. [/quote] More crap. This App doesn't have the ability to harvest data from your iPhone. It simply takes credentials you supplied to access Instagram and then sends these to their own servers as well.