Efforts by the FBI and certain lawmakers seeking to ban Apple and other U.S. companies from selling products with real encryption will not be effective, note researchers in a study citing 865 encryption products already available in 55 countries— two thirds of which originate outside the U.S.
Why encryption backdoors don't make sense
The study for Harvard University's Berkman Center for Internet and Society, conducted by cryptography expert Bruce Schneier and colleagues Kathleen Seidel and Saranya Vijayakumar, surveyed the availability of encryption products worldwide, compiling findings that make it clear that U.S. laws to weaken domestic encryption wouldn't stop malicious users from obtaining foreign encryption, but would put U.S. firms at a competitive disadvantage.
Schneier noted that an earlier form of the same findings were published back in 1999, when the Federal Government was considering whether to continue classifying strong encryption as a "munition" banned for export outside the U.S.
IN 1997, the FBI's director Louis Freeh had testified to the US. Senate Judiciary Committee that without backdoors, the export of real encryption products "ultimately will devastate our ability to fight crime and prevent terrorism. Uncrackable encryption will allow drug lords, spies, terrorists and even violent gangs to communicate about their crimes and their conspiracies with impunity."
However, Schneier's report showed that restricting the export of real encryption products "had done nothing to reduce their availability around the world," but was making it harder for U.S. firms to compete globally.
Seventeen years later, an updated version of the same survey discovered 546 foreign encryption products, "44% of which are free," and "34% are open source."
It noted, "there is no difference in the advertised strength of encryption products produced in or outside the US. Both domestic and foreign encryption products regularly use strong published encryption algorithms such as AES. Smaller companies, both domestic and foreign, are prone to use their own proprietary algorithms."
The report added, "some encryption products are jurisdictionally agile. They have source code stored in multiple jurisdictions simultaneously, or their services are offered from servers in multiple jurisdictions. Some organizations can change jurisdictions, effectively moving to countries with more favorable laws."
It further concluded, "anyone who wants to evade an encryption backdoor in US or UK encryption products has a wide variety of foreign products they can use instead: to encrypt their hard drives, voice conversations, chat sessions, VPN links, and everything else.
"Any mandatory backdoor will be ineffective simply because the marketplace is so international. Yes, it will catch criminals who are too stupid to realize that their security products have been backdoored or too lazy to switch to an alternative, but those criminals are likely to make all sorts of other mistakes in their security and be catchable anyway.
"The smart criminals that any mandatory backdoors are supposed to catch— terrorists, organized crime, and so on— will easily be able to evade those backdoors."
Apple on encryption
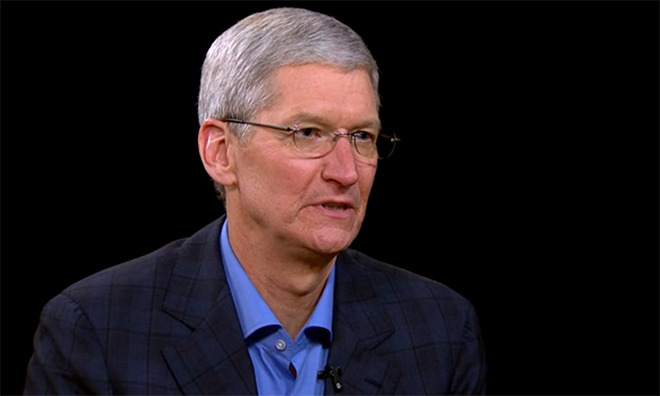
Apple's chief executive Tim Cook has made privacy— and the encrypted security protecting users' privacy from corporate, government or terrorist snooping— into a key issue.
A year ago, Cook stated in an interview that "none of us should accept that the government or a company or anybody should have access to all of our private information," adding, "This is a basic human right. We all have a right to privacy. We shouldn't give it up. We shouldn't give in to scare-mongering or to people who fundamentally don't understand the details."
"Terrorists will encrypt. They know what to do," Cook said. "If we don't encrypt, the people we affect are the good people. They are the 99.999 percent of people who are good."
He added, "You don't want to eliminate everyone's privacy. If you do, you not only don't solve the terrorist issue but you also take away something that is a human right. The consequences of doing that are very significant."
In January, Cook reiterated his stance that "any backdoor means a backdoor for bad guys as well as good guys" at a security summit attended by FBI director James Comey and a variety of counterterrorism advisors including the National Security Agency.
There ought to be a law!
The magical allure of being able to tap into the encrypted messages of terrorists and other criminals has remained a political football. In the UK, Prime Minister David Cameron joined proponents of an Investigatory Powers Bill intended to force companies to include software backdoors and enable forced access to encrypted devices when requested by the police.
Apple issued a formal challenge to the legislation in December, stating that "the creation of backdoors and intercept capabilities would weaken the protections built into Apple products and endanger all our customers. A key left under the doormat would not just be there for the good guys. The bad guys would find it too."
That same month, U.S. Senator Tom Cotton, a Republican from Arkansas, appeared on 60 Minutes to vilify Cook's message, stating that with effective encryption, companies like Apple, Google and Facebook can be expected "to become the preferred messaging services of child pornographers, drug traffickers, and terrorists."
Last month in New York, the state assembly considered a bill seeking to demand that any phones sold in the state "be capable of being decrypted and unlocked by its manufacturer or its operating system provider." California also considered a similar bill.
Earlier this week however, the ENCRYPT Act, sponsored by House Democrat Ted Lieu and Republican Blake Farenthold, was crafted at the federal level to bar individual states and localities from requiring backdoors in encryption.
Encryption and terrorism
In 2014, the the Electronic Frontier Foundation reported that among consumer security products, Apple's iMessage and FaceTime "stood out as the best of the mass-market options,"
The EFF also noted that competing products, including AIM; BlackBerry Messenger; Facebook's Messenger and WhatsApp; Google Chat and Hangouts; Microsoft's Skype; Secret; SnapChat and Yahoo Messenger all failed to provide similar end-to-end encryption to Apple's.
A year later, an OPSEC manual was discovered being distributed among supporters of the Islamic State, recommending the use of Apple's iMessage as being securely encrypted, unlike most other American products.
However, ISIS terrorists behind the recent Paris attacks were using unencrypted channels to coordinate, and there's no evidence that ISIS is actually using iMessage, as the OPSEC manual was originally written for journalists operating in Israel and Gaza by researchers in Kuwait. ISIS operates across a series of regions where iPhones have very low penetration.
Middle Eastern terrorist groups like ISIS and Al Qaeda overwhelmingly use cheap, commodity products due to the "large availability and affordability of Android phones, especially in underdeveloped countries," and know how to equip them with third party encryption software outside the jurisdiction of U.S. or U.K. laws.
"If you halt or weaken encryption," Cook warned, "the people that you hurt are not the folks that want to do bad things. It's the good people. The other people know where to go."