Mac malware discovered in Microsoft Word document with auto-running macro
A second example of malware targeting macOS users has surfaced this week, with the discovery of a Word document that attempts to use an automatically-running macro, one that tries to download a hazardous payload to infect the target Mac.
The Word file, titled "U.S. Allies and Rivals Digest Trump's Victory - Carnegie Endowment for International Peace" is noted in research compiled by Objective-See to show a usual Word macro warning when it is attempted to be opened by potential victims. The notice warns that macros could contain viruses, and gives the option to continue opening the file with and without macros enabled, as well as to back out from opening it at all.
If run with macros enabled, the automatic macro starts to run python script, which first checks if network monitoring tool Little Snitch is running, before attempting to download a second-stage payload from a specific URL, decrypting the payload, and then executing its contents. The python code itself is sourced from the open-source EmPyre project, an existing post-exploitation framework, with the code used "almost verbatim."
While the payload file is now inaccessible, making it impossible to know what exactly happened to victims, researchers found some second-stage components of EmPyre code that hints at what would take place. It is thought the payload would try to persist on the Mac, automatically running after a reboot, and then could perform functions based on one of many EmPyre modules.
The infected Word file is entitled "U.S. Allies and Rivals Digest Trump's Victory - Carnegie Endowment for International Peace"
These modules offered a multitude of options for attackers to acquire data, including keyloggers, Keychain dumps, clipboard monitoring, taking screenshots, accessing iMessage, and even an attached webcam.
The malware "isn't particularly advanced," suggests security researcher Patrick Wardle of Synack, due to requiring interaction from users to open the document and needing macros to be enabled. The file's creators does receive some credit from Wardle, by exploiting users as "the weakest link" in security, while also taking advantage of the "legitimate" functionality of macros making it an infection vector that "doesn't have to worry about crashing the system nor being 'patched' out."
Malware embedded in documents is a relatively old technique of infection, largely affecting Windows users rather than Mac, and despite relying heavily on the user disregarding the initial warning notice, has found some success in the past. The notable Melissa virus of 1999 used a Word macro to infect systems, sending copies of the file to a number of the user's contacts to spread.
This infected Word document arrives at the same time as one other type of macOS malware. MacDownloader, malware believed to have been created by Iranian hackers, used a fake aerospace website with a falsified Flash update, to try and attack members of the U.S. defense industry and human rights advocates.
 Malcolm Owen
Malcolm Owen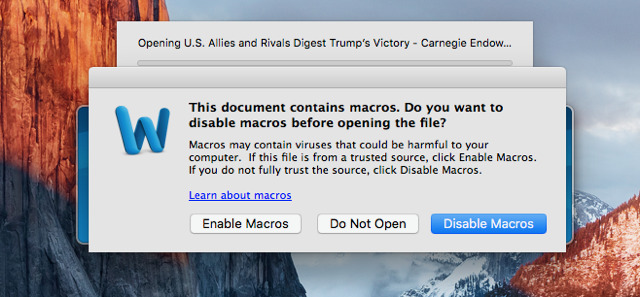













 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly
 AppleInsider Staff
AppleInsider Staff
 William Gallagher
William Gallagher

 Christine McKee
Christine McKee










15 Comments
So in other words, still Microsoft's fault.
One big problem/annoyance with MS Office macros is that when you get the warning, you don't have any other information about what the macro is. There are legitimate uses for macros, meaning you can't always keep macros turned of completely. Still, I can't think of many that would require the level of access used by this exploit, so it would be helpful if Microsoft limited the abilities of macros to do so, and getting a file like this with a macro built in should be a huge red flag.
Yay. MS Word on Mac is now more like on Windows.
Yay. Macs are now used enough to be targeted by malware on a regular basis.