A number of vulnerabilities have been revealed in Amazon's Alexa, highlighting the need for providers of smart home platforms, such as Apple's HomeKit, to maintain security as part of the service.
The concept of a smart home is attractive, but the dream of ordering a virtual assistant around to automate household tasks becomes a nightmare once security issues surface. In the case of Amazon's Alexa, which is at the heart of many people's smart home setup, vulnerabilities have been revealed that could have allowed an attacker to perform tasks and to find out what a user has told Alexa, issues that have since been fixed.
The report from Check Point Security researchers reveals a number of Amazon and Alexa subdomains were vulnerable to a Cross-Origin Resource Sharing (CORS) misconfiguration and Cross Site Scripting (XSS). By using XSS, an attacker would be able to acquire a CSRF token that would provide them access to elements of the smart home installation.
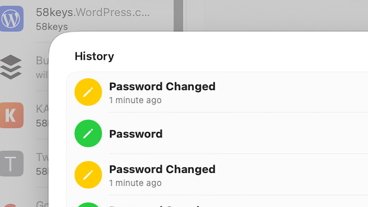
According to the researchers, these could include automatically installing Alexa skills without the knowledge of the user, acquiring a list of all installed skills, silently removing installed skills, acquiring the victim's voice history with Alexa, and to even gain personal information.
This skill manipulation could have allowed for a modified version of an existing skill to be installed and then used by the user, one that could allow actions to be performed by the attacker, or for further acquisition of data from the user. It could even have been possible for an attacker to install a skill to eavesdrop into conversations near an Echo device.
While eavesdropping would have been possible, users had the potential tip-off of something untoward as listening would have triggered the blue light indicator on the Echo device.
Users are normally able to monitor and delete their voice history via the Alexa Privacy Settings page, or the Alexa app. Users can also wipe records by saying "Alexa, delete what I just said" or "Alexa, delete everything I said today," while an automated deletion option can wipe the data once it is three months or 18 months old.
It is claimed a successful exploitation of the vulnerabilities would have been possible through a single Amazon link click by the victim.
Check Point responsibly disclosed the vulnerabilities to Amazon in June 2020, and the issues have been fixed.
"Internet of Things devices are inherently vulnerable and still lack adequate security, which makes them attractive targets to threat actors," Check Point writes. "Cybercriminals are continually looking for new ways to breach devices, or use them to infect other critical systems. This research presented a weak point in what is a bridge to such IoT appliances. Both the bridge and the devices serve as entry points. They must be kept secured at all times to keep hackers from infiltrating our smart homes."
"The security of our devices is a top priority, and we appreciate the work of independent researchers like Check Point who bring potential issues to us," said an Amazon spokesperson. "We fixed this issue soon after it was brought to our attention, and we continue to further strengthen our systems. We are not aware of any cases of this vulnerability being used against our customers or of any customer information being exposed."
Amazon has courted controversy with the security and privacy issues of its smart home platform in the past. In 2019, it was found Amazon employees were listening to audio recordings from Echo devices to improve its accuracy, while later in the same year researchers were able to add spying apps to app stores for Alexa and Google Home that enabled eavesdropping and phishing to take place.
While Apple does operate its own HomeKit smart home platform, the company does work to keep each element as secure as feasibly possible. This includes extensive use of encryption, as well as a long list of requirements and restrictions each new HomeKit-compatible device must abide by to function on the platform.
Update: August 18: Updated with Amazon statement and minor changes.