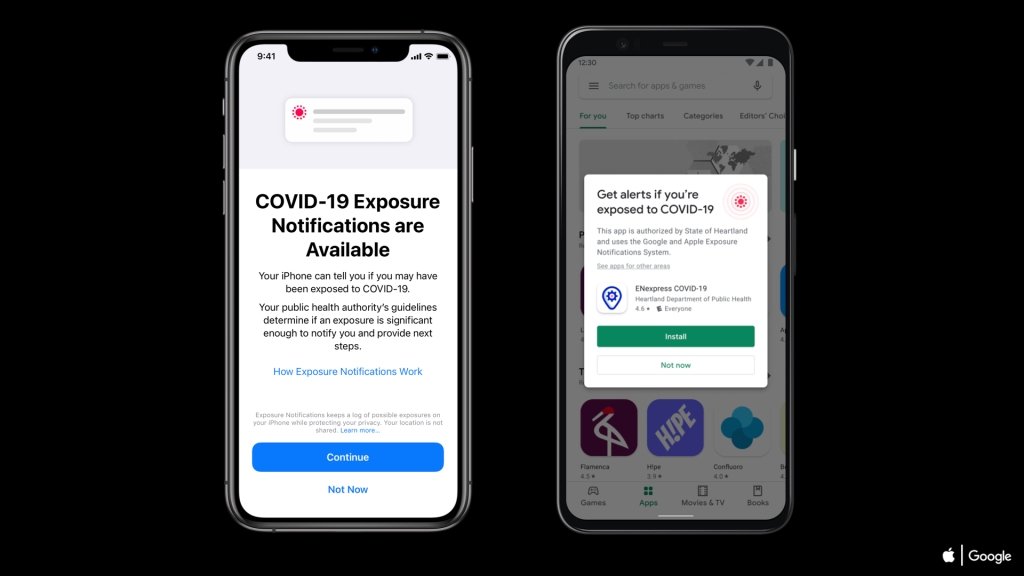
The Android version of the Apple and Google Exposure Notification system reportedly has a flaw that may have leaked sensitive data to a device's preinstalled apps.
Back in 2020, the two tech giants unveiled the collaborative project as a way to help mitigate the spread of coronavirus. Although Apple and Google promised that the system would be privacy-respecting, a new report suggests that may not be the case on Android.
According to The Markup, a flaw in the system could let preinstalled apps on an Android device see sensitive information, such as if a user has been in contact with another person who tested positive for COVID-19.
The issue lies in the fact that contract tracing data is stored in privileged system memory on Android devices. While that memory is normally inaccessible to other apps, preinstalled apps from manufacturers can see those logs because of special privileges. There is no indication that any apps have abused the flaw, however.
App privacy analysis firm AppCensus discovered the flaw and reported it to Google in February. As of Tuesday, the issue has yet to be resolved.
Google says that updates to fix the issue are currently "ongoing." However, according to AppCensus, fixing the issue would only require deleting a few "nonessential" code strings.
According to The Markup and researchers at AppCensus, the iPhone version of the exposure notification system does not have any similar vulnerabilities.