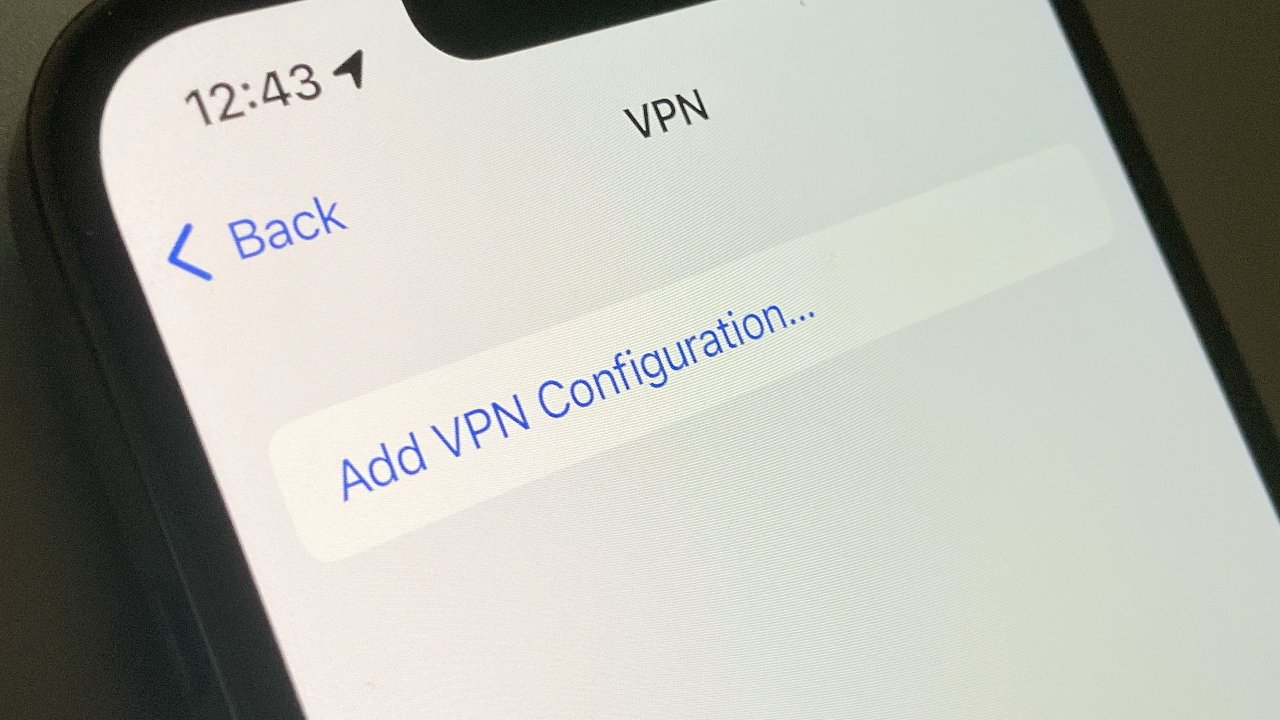
A detailed new report says that a long-time bug in iOS prevents any VPN from fully encrypting all traffic — and also claims that Apple has known about it and chosen to do nothing since discovery in 2020
The vulnerability was first discovered by VPN firm ProtonVPN in March 2020. At the time, the company said that when a VPN is switched on, the OS should terminate all internet connections and automatically re-establish them via the VPN to prevent unencrypted data leakage.
In iOS 13.3.1 and later versions, devices connecting with a VPN didn't close and re-open connections. Consequently, it was possible that a user would unknowingly in part continue to use the insecure connection they had before turning on the VPN.
"Those at highest risk because of this security flaw are people in countries where surveillance and civil rights abuses are common," said the company at that time.
Now Michael Horowitz, who describes himself as an independent computer consultant and blogger, says the vulnerability still exists. In a copiously illustrated 7,500 word post about the issue, Horowitz repeatedly found significant data leaks when using VPNs on iOS.
"It takes so little time and effort to re-create this, and the problem is so consistent, that if [Apple] tried at all, they should have been able to re-create it," he writes. "None of my business. Maybe they are hoping, that like ProtonVPN, I will just move on and drop it. Dunno."
In short, Horowitz looked at the data stream that was exiting the iPad while different VPNs were being used.
"At first, they appear to work fine," he writes. "But, over time, a detailed inspection of data leaving the iOS device shows that the VPN tunnel leaks."
"Data leaves the iOS device outside of the VPN tunnel," continues Horowitz. Using a newly-updated iPad and turning on a VPN, he recorded what he described as "another flood of requests... travelling outside the VPN tunnel."
Horowitz stopped after repeatedly documenting similar issues.
"I am simply interested in whether there is a problem, yes or no," he said. "I am not interested in fully defining/debugging the problem. That's for Apple."
Horowitz's detail includes his failed attempts to discuss the issue with Apple and the government's Cybersecurity and Infrastructure Security Agency (CISA).
"At this point, I see no reason to trust any VPN on iOS," he concludes. "My suggestion would be to make the VPN connection using VPN client software in a router, rather than on an iOS device."
Horowitz's research has concentrated on the use of third-party VPNs. He has not reported on whether there are any issues using Apple's Private Relay. Apple doesn't consider the Private Relay to have the same functionality as a full VPN, however. You can find a list of the cheapest VPN deals and our favorite VPN for iPhone picks in our dedicated roundups.