Mac & Windows owners have to contend with different kinds of malware
If you have a Mac, you have different types of malware attacks to worry about versus what Windows owners have to contend with most of the time. Here are the main differences.
According to the report, Malwarebytes believes that the threats to cybersecurity are changing and that attackers are switching up their strategies.
Instead of relying on old methods, like employing macros in Word documents or exploiting weaknesses in Flash, attackers now employ psychological manipulation to gain access to the data they want.
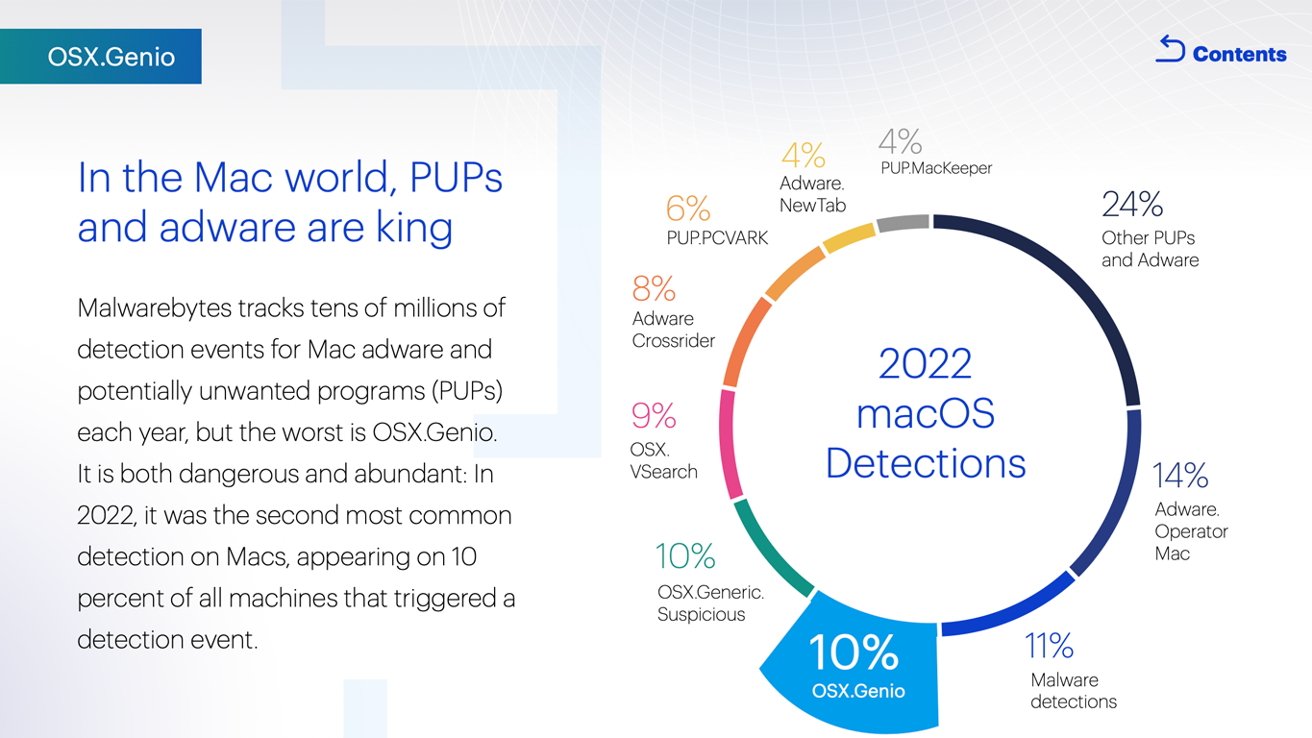
When it comes to Macs, macOS is more likely to suffer from "deceptive, sophisticated, hard-to-remove adware." than other types of malicious attacks. In fact, about 10% of all detections on macOS were from adware called OSX.Genio.
Like many types of adware, Genio highjacks a user's browser and uses it to inject its own ads into their search results.
While technically adware, OSX.Genio behaves more like malware. It exploits a system vulnerability "to grant itself elevated permissions; manipulating users' keychains; and installing browser extensions without consent."
More broadly, Malwarebytes notes that ransomware is on the rise. In 2022 alone, 71% of companies were affected by ransomware in some capacity, 10% more than the previous year.
The most dominant ransomware of 2022 was the Windows-centric LockBit, which accounted for a third of ransomware-as-a-service (RaaS) attacks. RaaS attacks are employed by those who do not develop the ransomware itself. If the attacker is successful, they pay a share of the money back to the ransomware's developers.
While RaaS events are rarer than other types of malware, the effects are often significantly more devastating. LockBit is spread through an affiliate-style program, allowing attackers to employ a targeted attack against an individual or company.
Malwarebytes points out that LockBit affected businesses of all sizes, "from local law firms with a handful of employees to multi-national enterprises."
The rest of the report covers influential events from 2022 that are shaping what is yet to come. This includes taking a look at cybersecurity during times of war, issues with passwords and authentication methods, and social engineering.
 Amber Neely
Amber Neely









 Thomas Sibilly
Thomas Sibilly
 AppleInsider Staff
AppleInsider Staff
 William Gallagher
William Gallagher
 Malcolm Owen
Malcolm Owen
 Christine McKee
Christine McKee









1 Comment
This may sound odd, but compared to the Windows and Android world, Mac and iOS users have it pretty easy. As the chart in the article shows, the vast majority of “threats” are related to extra ads, search redirects, and other malware I’d classify as “annoyware” rather than actual threats.
There are some alarming pop ups that claim your computer is insecure and you need to call “Mac” or “Apple” (or, more often, “Windows Support”) so you can get scammed, but these are usually the result of a user mistyping a web address or clicking on clickbait headlines. There’s also email scams, but they are generally pretty easy to spot unless you’re not paying attention/fairly gullible to “too good to be true” offers.
The one and ONLY anti-malware product I can wholeheartedly recommend is MalwareBytes. It catches things all the other ones miss (especially now that BrowserGuard is working properly), and is cheaper than any other others to boot. You can even use it (reactively) for free if you want to try it out for more than the two week free trial (the paid version is PRO-active, preventing things from getting in in the first place, and thus I recommend going for it).