Two-factor Authentication requires you to use a personal device that isn't the device you're using when you log in to enhance security. Here are the best ones for iOS 16.
Given the wide range of security threats and breaches on the internet, it's more important than ever for you to protect your accounts and data online.
Two-factor Authentication (2FA) is a way to insure that only you have access to your accounts by means of a second way of verifying who you are when you login.
In 2FA, typically you log in with a password as usual, but then the online system you are logging in to contacts you back to ask you to verify yourself. This is usually accomplished via an email, or a special one-time code (OTC) that is sent to you via email, text, phone call.
Once you have the OTC in hand, you use it to essentially confirm to the system that you are who you say you are. Once you enter the code that was sent to you, authentication is completed and you are authorized to use the system.
Most banks and online payment services such as PayPal and auction sites such as eBay and others now use 2FA when you log in.
One of the reasons 2FA is more secure than plain passwords is you must have the device the secret code is sent to in your possession in order to complete login: if someone else tries to log in claiming to be you, they will be denied by the system since they don't have your phone, tablet, or access to your email account.
2FA makes login more secure by requiring an extra step in the login process sent in real-time by the system you are logging into itself. It's not foolproof, but it's much more secure than merely a single password.
Two-factor authentication apps and QR codes
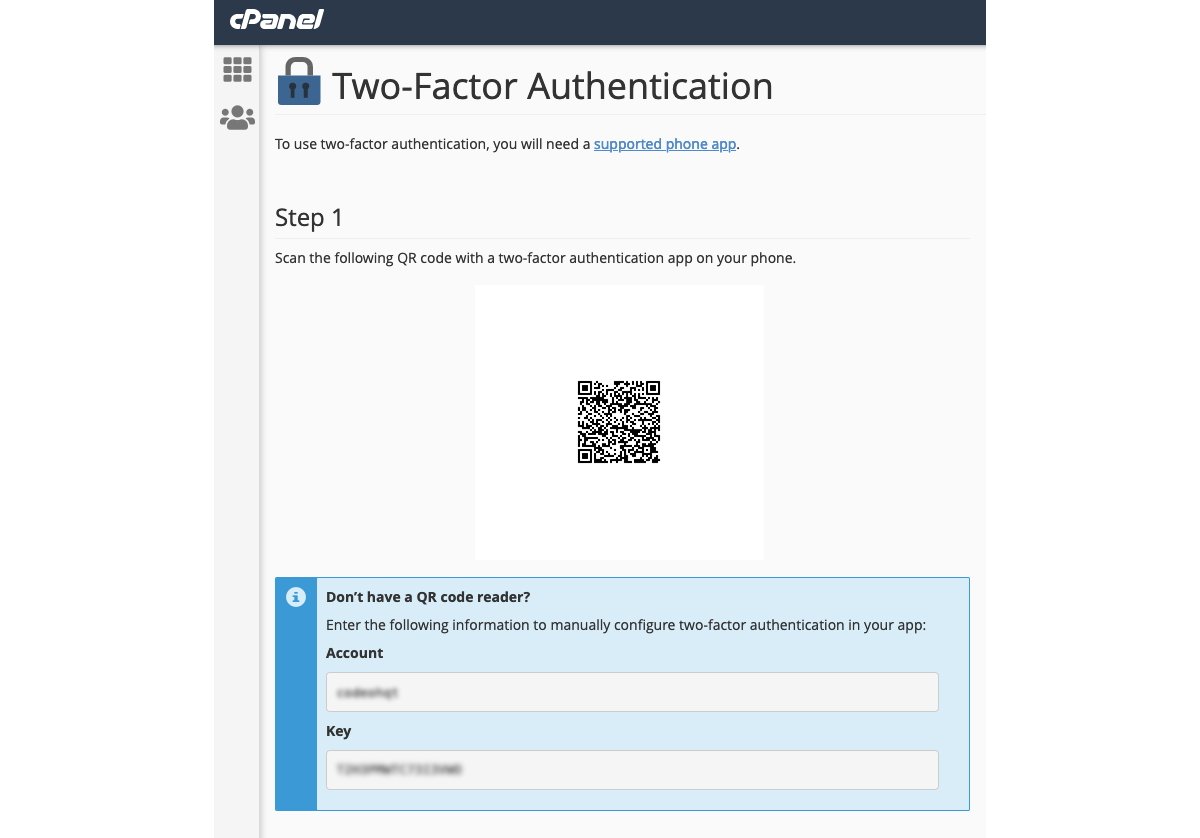
To take the 2FA idea a step further, there are now a host of apps you can install on your personal device, each if which receives and stores a secret code for each system you want to log into in the future. The codes usually expire quickly so they can't be stolen and used by others.
The first time you log in to each online system, it may ask you to scan on your mobile device a QR code it presents on your computer, or it may send you a 2FA code for future use. Each code gets stored in the app for later use.
The 2FA app knows which codes belong to which systems so you don't have to remember them. Most of the set up is automatic on the backend.
The idea behind 2FA apps is that the app acts as a storehouse for all your secret codes. The next time you want to log in to a given system, you simply look the code up on your mobile device and enter it into your computer, or use it to scan a new QR code presented on the system at login time.
The app's backend infrastructure then notifies the system that you are trying to log in and that you are who you say you are.
2FA apps act as sort of a broker - authentication always happens on a third-party system, never on the system you are trying to log in to. This is considered good security practice.
In most cases, the backend systems involved pass an authorization token between each other for the login session. If the token times out out, you'll likely be asked to log in again. All of this happens invisibly on the backend.
Once you verify your secret code using your 2FA app, its backend tells the system you want to log in to that everything is ok and to proceed. This is the kind of tokenized login process that that happens, for example, when you purchase something on eBay and then pay for it with PayPal online.
2FA apps merely extend a similar system design one step further by storing your secrets needed to log in.
Which two-factor authentication app is best?
There are dozens of 2FA apps on the market. Some are free, some you have to pay a service to use.
Major internet players such as Google and Microsoft have 2FA authenticator apps, as does Oracle, 2Stable, and others. Some 2FA apps such as Authy and others require to you sign up first on their website and provide personal info including your phone number. Others don't.
2Stable also provides an Apple Watch authenticator app.
Google Authenticator is simple, but doesn't provide any built-in way to backup your 2FA data or secrets.
On iOS, some 2FA apps also support FaceID and TouchID, others don't.
Duo Mobile, which was acquired by Cisco Systems, is intended more for corporate use.
LastPass is another major player in the third-party 2FA app arena, but the company's password manager service was recently hacked and it has admitted user's password vaults have fallen into the hands of hackers as a result.
Note that LastPass has both a 2FA and a password manager app. The two are different. Password manager is for storing passwords, the 2FA app is for secrets used only in 2FA.
By far, the most popular of the free 2FA apps is 2FAS.
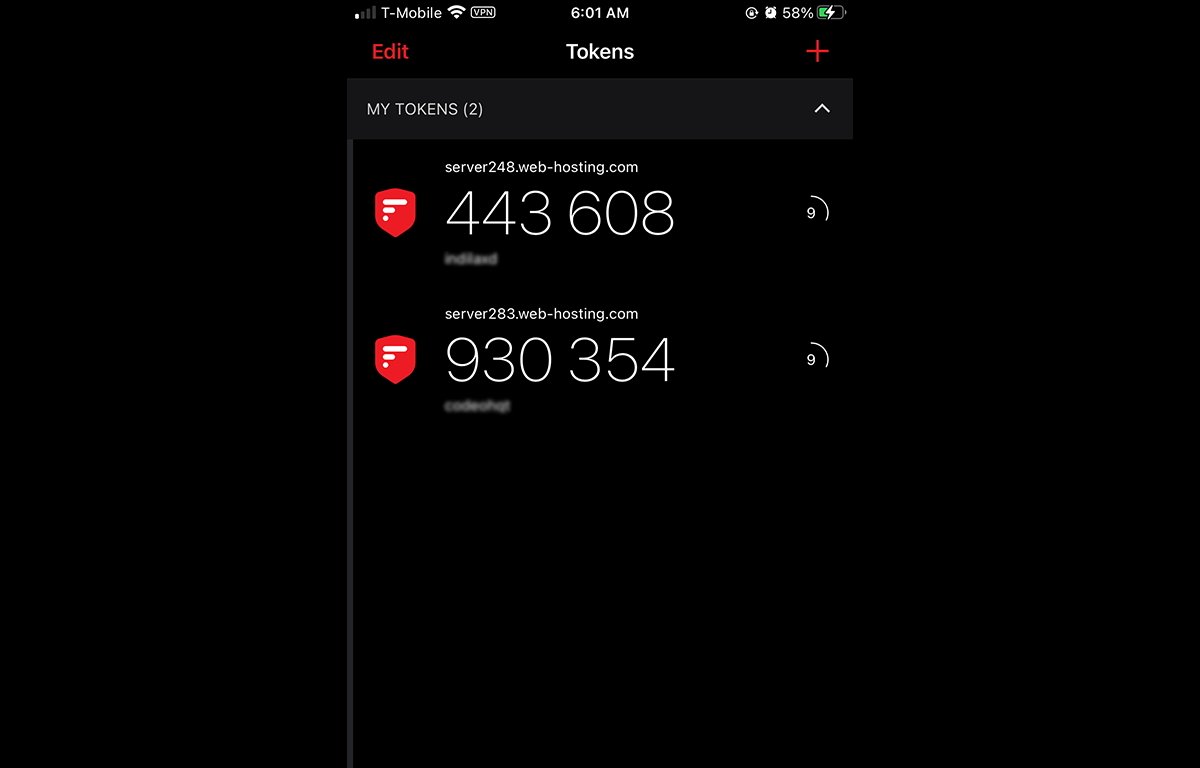
2FAS is easy to set up and use, provides a simple scrolling list of timed secrets, and adding new services or websites to it is a breeze. For example, many web hosting companies now support 2FAS for login authentication, which you only need set up once.
This usually involves scanning an automated QR code when turning on 2FA on your web hosting control panel, which you then scan on your phone using the camera. 2FAS recognizes the QR code, and generates a unique six-digit OTC every 30 seconds for each service when viewing the app on your mobile device.
From then on, no one can log in to your web hosting account unless they have both your login password, and your mobile device. 2FAS also offers an Android version.
Most other websites that support 2FA work in a similar manner.
Most of the secret codes stored in 2FA apps expire very quickly - within thirty seconds or so, and then reset themselves in the app automatically. This prevents any codes which may have been compromised from remaining valid for very long.
You basically have under a minute to use the displayed codes or they become invalidated. This also prevents anyone else from writing the codes down and using them later.
Apple Watch apps
Some 2FA apps offer an Apple watch app: as of this writing Authy and Microsoft Authenticator offer an Apple Watch version of their 2FA apps, Google and LastPass don't.
Encryption
Most of the 2FA apps support encryption during sync and backup, but surprisingly, as of this writing neither Microsoft Authenticator nor Google Authenticator do. Some 2FA apps such as TOTP Authenticator do, but only during backup.
Two-factor authentication on the Mac
As a side note, you can also use 2FA on the Mac - using Apple's login system, Face ID, or Touch ID which is now standard on most Apple devices including on most current Mac keyboards. Logging in to most Apple online systems such as Apple ID will generate a 2FA one-time code (OTC) which you must enter on another Apple device in order to log in.
If you only own one Apple device, Apple will send the OTC to the same device, which sort of defeats its purpose if your device falls into the wrong hands. Face ID and Touch ID, obviously eliminate this failing.
Third-party hardware companies such as Yubico sell plug-in USB devices, which use your fingerprint to authenticate you, much like Apple's Touch ID does.
Google sells similar biometric USB-based keys called Titan Security Key, which essentially work the same as Yubikey.
Hardware biometric authentication is always more secure than mere software authentication because you must have the physical device - and your fingerprint or face present to authenticate. Biometrics add an extra layer of security to 2FA, making it 3FA: you are a third key.
Choose wisely
Most of the 2FA apps are on par with each other, aside from the minor issues mentioned above. Most don't have any major problems - if they did they would be considered a security risk and would be pulled from the Apple and Google app stores quickly.
By far the most popular and successful third-party 2FA apps are 2FAS and Authy by a clear margin with Duo Mobile the leader for corporate use.
2FAS and Authy are simple and easy to set up, 2FAS doesn't require your phone number or even an email to set up, and neither app causes hassles. Both are straightforward.
You can't really go wrong with a 2FA app. If your app doesn't use real-time codes, just be sure to back up your secrets in a way that allows you to access them later if you need to - if you lose access to your secrets, it's likely you'll be locked out of your 2FA-enabled accounts.
 Chip Loder
Chip Loder








 Andrew Orr
Andrew Orr
 Malcolm Owen
Malcolm Owen
 William Gallagher
William Gallagher
 Wesley Hilliard
Wesley Hilliard




-xl-m.jpg)


-m.jpg)



