Face ID
All about Face ID
Table of Contents
Apple introduced Face ID as a successor to Touch ID, although it hasn't replaced the fingerprint on every device. It is deemed as more secure with a fail rate of 1 million to 1 versus Touch ID with a fail rate of 50,000 to 1.
In 2022, Apple introduced a new feature for iOS 15.4 that lets people use Face ID while wearing medical masks. It relies on the area around a person's eyes for identification rather than the entire face.
While this feature is a boon for those frequently wearing masks, it is less secure than standard Face ID. Those who own an Apple Watch should use the Apple Watch unlock feature instead.
Face ID features
Face ID uses a set of technologies to scan a user's face in real-time and convert it to a mathematical representation for verifying a user's identity. It is used to unlock the device, make payments, and secure some apps.
Apple only makes Face ID available on the iPad Pro and most iPhone models. Other iPads use some form of Touch ID while Macs use Touch ID in the Magic Keyboard.
TrueDepth system
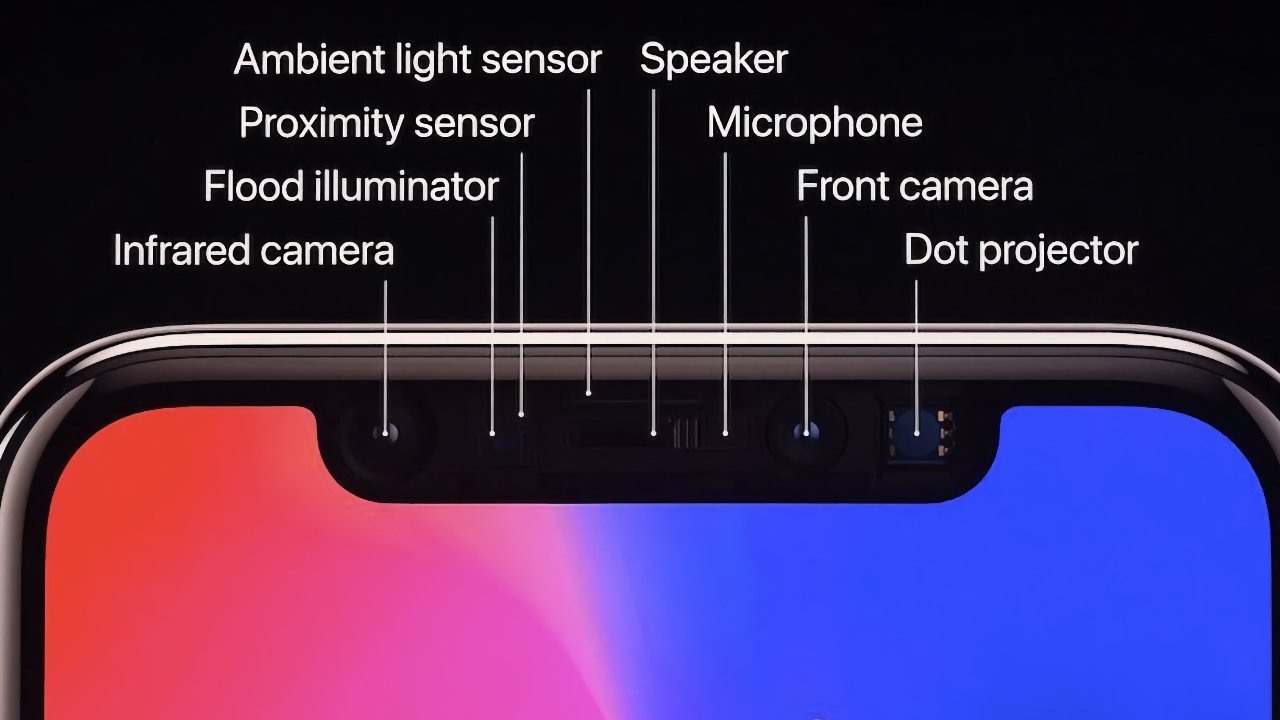
The TrueDepth system is comprised of six components dedicated to detecting and scanning a face. It is used for Face ID primarily, but other features like Memoji take advantage of the technology.
The infrared camera looks for a face when motion is detected. If one is found, the proximity and ambient light sensors determine the amount of light needed for face recognition. A flood illuminator then captures 2D images of the user's face.
The dot projector casts 30,000 dots across the user's face to construct a 3D depth map and uses the 2D infrared images as a reference.
The combined data is processed by the application processor and converted into a numerical value and encrypted using machine learning algorithms. This value is compared to a value stored within the Secure Enclave to determine if the scanned face matches the one in the database.
When a device is locked, the TrueDepth system automatically activates when owners tap the screen, raise the device, or when a notification wakes the screen. When the user attempts to unlock the device, the TrueDepth system captures a new image.
Apple reduced the size of the notch, then ditched it entirely. The iPhone 14 Pro lineup uses the same sensors, but they fit within a smaller area and are obscured using software called the "Dynamic Island."
This system works with hats, glasses, many sunglasses, and scarves. Significant changes require the user to re-enroll their face, like shaving off a heavy beard. Apple states that the stored data is refined and updated each time users successfully unlock the device using face recognition. Additionally, this system updates the data if face recognition only finds a close match and forces the user to enter a passcode.
Apple recommends using a passcode for children ages 13 and under, for twins, and users with near-identical siblings. Face ID requires the user to establish a passcode for when facial recognition isn't possible, or after five failed attempts.
Secure Enclave
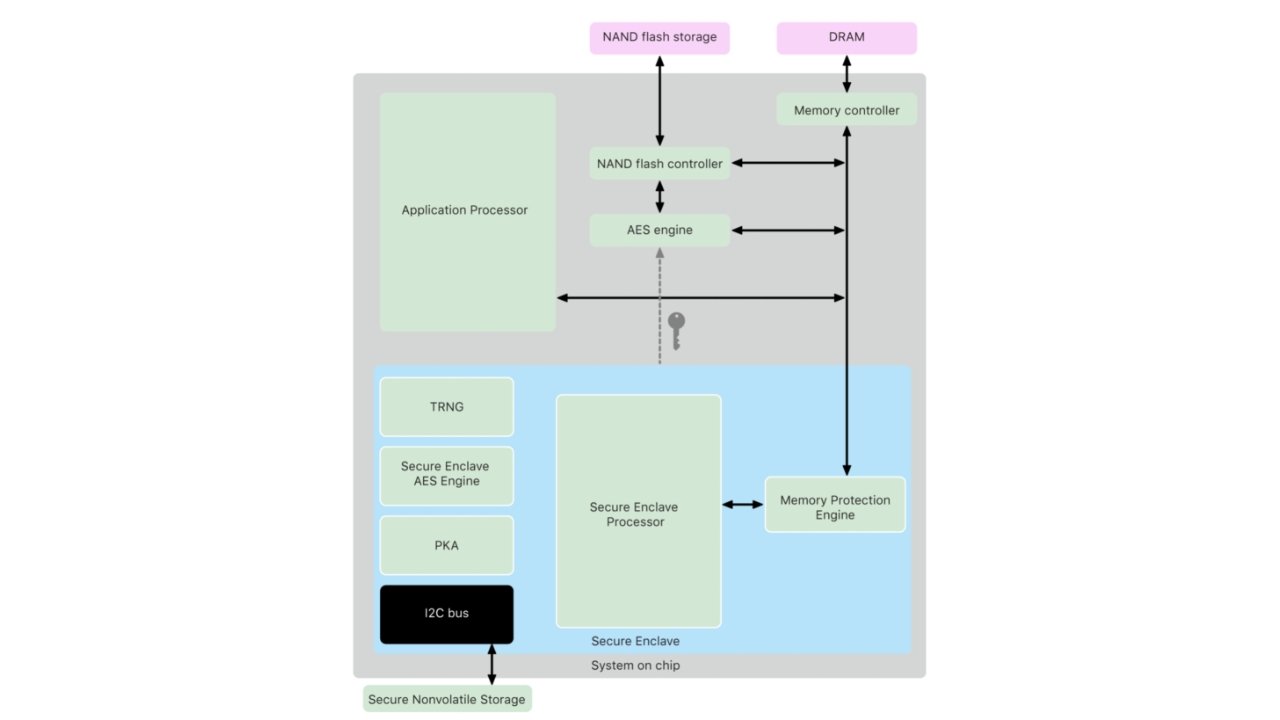
The Secure Enclave is a coprocessor that physically resides within the Apple Silicon package, like the A15 or M1. It is isolated and communicates directly with the parent chip using an interrupt-driven "mailbox." The Secure Enclave and parent chip also share memory data buffers. Because the Secure Enclave is isolated and self-maintaining, it retains its integrity even if iOS or iPadOS is compromised.
According to Apple, it runs a custom version of the company's L4 microkernel (firmware) that's digitally signed by Apple and verified during the hardware boot chain process.
A portion of the neural engine is protected within the Secure Enclave. This machine-learning algorithm converts data provided by the TrueDepth platform into mathematical representations. These numbers are encrypted and stored in the file system, as the Secure Enclave's 4MB of storage is only used for 256-bit elliptic curve private keys.
When a file is created on the device, the AES engine generates and uses a new 256-bit "per-file" key to encrypt the data as it's written to the flash storage. This key is then encrypted using a class key and stored in the file's metadata, which in turn is encrypted with a random file-system key created when iOS or iPadOS was first installed.
The Secure Enclave stores the class key and handles all wrapped file keys, meaning these keys are never revealed to the application processor. On devices that use the Apple File System, the file-system metadata key is encrypted using the Secure Enclave's Hardware UID (Unique Identifier) key. The SoC's firmware encrypts all keys stored within the Secure Enclave.
Using biometrics
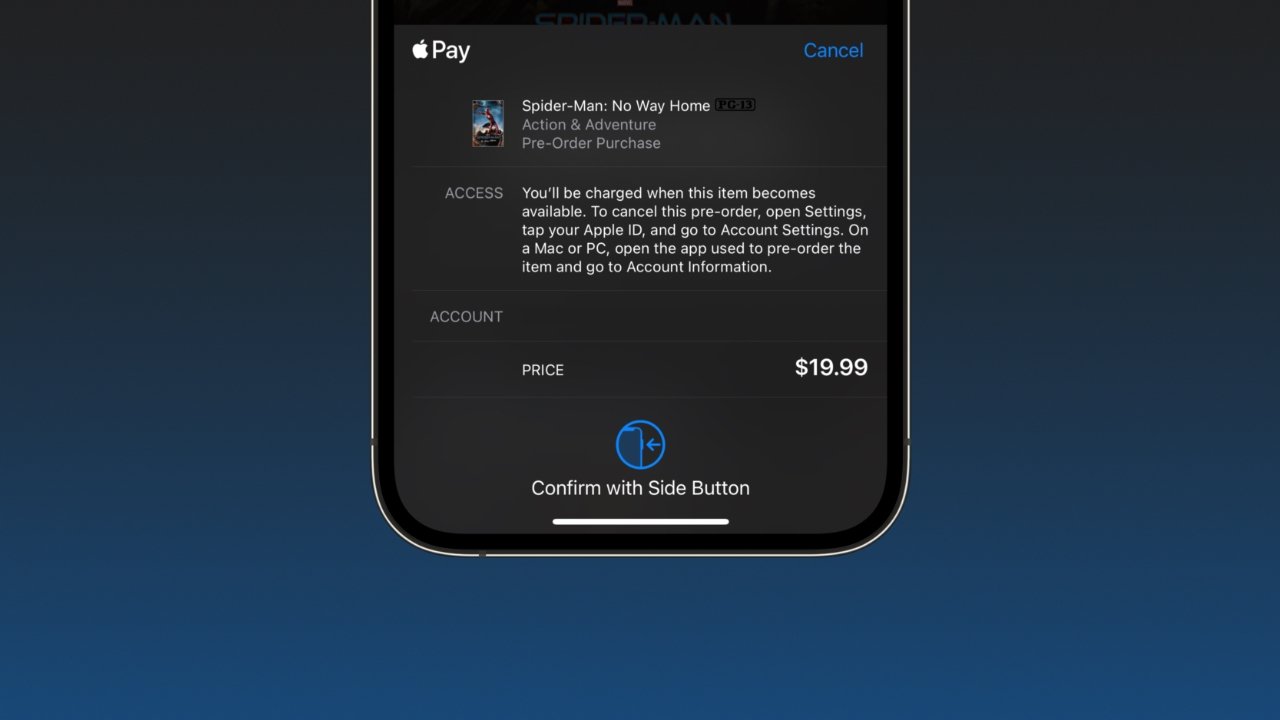
Face ID is used for more applications than just unlocking a device. It is integrated throughout iOS and iPadOS for secure access to information and payments.
Developers can add support for biometrics to keep unauthorized users from snooping around apps that could contain sensitive information. This has been a popular option for banking apps and some file storage clients.
Users can also make purchases using Face ID as an authentication tool. This can occur on the web, in an app, or in the App Store. To prevent abusive tactics by developers or scammers, Apple always requires the side button to be double pressed to authenticate a purchase.
The system is also used when accessing iCloud Keychain for password auto-fill in Safari. Certain sections in the Settings app are also secured with Face ID, like Passwords.
Two versions of Face ID
Apple has finally addressed user frustration with Face ID during the COVID-19 pandemic. In iOS 15.4 and later, users can set up an alternative version of Face ID that uses only the region around a user's eyes to authenticate.
The normal version of Face ID requires a person's eyes, nose, and mouth to be visible before authenticating. The new optional mask-friendly version uses a much smaller surface area of the face to authenticate, so it is less secure overall.
When a mask is detected, Apple also allows users to unlock their iPhone with an already-unlocked Apple Watch. When set up, if the TrueDepth system detects a mask, it skips trying Face ID and uses the Apple Watch within proximity to unlock the phone. This is the more secure option when paired with the original version of Face ID.