Apple working on software to detect and remove Flashback trojan
The Cupertino, Calif., company made mention of the upcoming tool in a support document regarding the malicious software, as noted by Jim Dalrymple of The Loop. The document also pointed users to last week's Java update that patched the security flaw that the virus was exploiting.
"In addition to the Java vulnerability, the Flashback malware relies on computer servers hosted by the malware authors to perform many of its critical functions. Apple is working with ISPs worldwide to disable this command and control network," the company said.
Apple also advises Macs running OS X 10.5 or earlier to disable Java in their browser preferences.
The Flashback trojan horse was first discovered last September. The malware posed as a phony Adobe Flash Player installer in order to trick users into installing it. At the time, a security first categorized the threat as "low." The current version of Flashback used the Java vulnerability to create a botnet that could mine personal information from unsuspecting users.
Evidence of Apple's efforts to contact ISPs surfaced earlier on Tuesday when a Russian security firm revealed that the company had targeted one of its servers as being "involved in a malicious scheme." Dr. Web chief executive Boris Sharov said the server was "not doing any harm to users" and was being used to monitor the spread of the virus.
Sharov noted that the relative rarity of Apple security issues meant that Dr. Web hadn't established close ties with the company. "For Microsoft, we have all the security response team’s addresses,†he said. “We don’t know the antivirus group inside Apple.â€
Last week, a Dr. Web analyst claimed that 600,000 Macs around the world had been infected by the Flashback malware. 56.6 percent of those infections are reportedly located in the U.S.
 Josh Ong
Josh Ong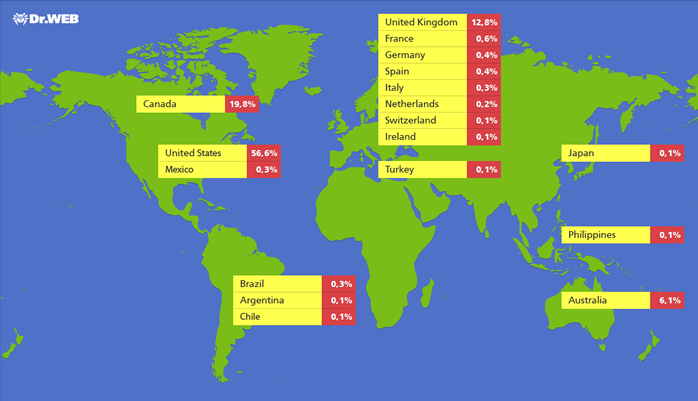








 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly
 AppleInsider Staff
AppleInsider Staff
 William Gallagher
William Gallagher
 Malcolm Owen
Malcolm Owen
 Christine McKee
Christine McKee










48 Comments
[...]The Flashback trojan horse was first discovered last September. The malware posed as a phony Adobe Flash Player installer in order to trick users into installing it.[...]
There's your problem, there. Nobody should install Flash. Period.
There's your problem, there. Nobody should install Flash. Period.
But it's a Java problem?
Fortunately, Apple already has software that takes care of it.
It's called LION. Neither Flash nor Java come with Lion.
As long as Apple distributes a version of Java, it must live up to its responsibilities to patch that version promptly with security updates. Patching a known security vulnerability 2 months after Oracle did is unacceptable.
Look for Apple to introduce zero tolerance in Mountain Lion.
But it's a Java problem…
Fortunately, Apple already has software that takes care of it.
It's called LION. Neither Flash nor Java come with Lion.
That's ridiculous. Why is Java updates distributed through the built-in Mac OS software update mechanism? Java may be third party software and no longer included in the latest Mac OS but it continues to be accorded special status by Apple. How did Apple distribute the Java updates that close this security hole? Not by telling you go to Oracle to download the update but sending it out through the OS software update.
As long as Apple distributes a version of Java, it must live up to its responsibilities to patch that version promptly with security updates. Patching a known security vulnerability 2 months after Oracle did is unacceptable.
Completely agree. Just as Microsoft is the keeper and bears responsibility for the security of the Windows platform, so Apple bears an equivalent obligation to work with third party software vendors - especially big ones like Oracle, run by Steve Jobs' best friend - to maintain the security of the Mac ecosystem. Its responsibility extends beyond the software it writes. Even John Gruber has now acknowledges that Flashback is an "epidemic" (because its infection rate is as big/bigger than the infection rate of the Windows Conflicker trojan) and a genuine problem. Pretending the "solution" to security holes is not to run software is ridiculous. Security holes area inevitable so they have to be patched quickly when found. Hopefully this will be bitter lesson for Apple to beef up their security practices.