At next week's Chaos Communication Congress in Germany, a researcher will demonstrate a method in which a malicious actor could use a specially-crafted Thunderbolt device to inject a bootkit — which could survive nearly any attempt to remove it — Â into the EFI boot ROM of any Mac with a Thunderbolt port.
The attack, discovered by researcher Trammell Hudson, takes advantage of a years-old flaw in the Thunderbolt Option ROM that was first disclosed in 2012 but is yet to be patched. In addition to writing custom code to the boot ROM, Hudson will also show a method by which the bootkit could replicate itself to any attached Thunderbolt device, giving it the ability to spread across even air-gapped networks.
Because the code lives in a separate ROM on the logic board, such an attack could not be mitigated by reinstalling OS X or even swapping out the hard drive. In the abstract for his presentation, Hudson also notes that he could replace Apple's own cryptographic key with a new one, preventing legitimate firmware updates from being accepted.
"There are neither hardware nor software cryptographic checks at boot time of firmware validity, so once the malicious code has been flashed to the ROM, it controls the system from the very first instruction," he wrote. "It could use SMM and other techniques to hide from attempts to detect it."
Vulnerabilities at such a low level are particularly troubling, as they are difficult to detect and can do significant damage. One previous demonstration of EFI hacking laid out a manner in which full-disk encryption systems such as Apple's FileVault could be bypassed with a bootkit, for instance.
Though Hudson's attack does require physical access, its ability to spread through other Thunderbolt devices makes it nonetheless quite dangerous. Users have a propensity to plug small, shared devices — such as display adapters — into their computers with little thought.
Hudson will take the stage to present his findings on Dec. 29 at 6:30 p.m. local time in Hamburg, Germany.
 Sam Oliver
Sam Oliver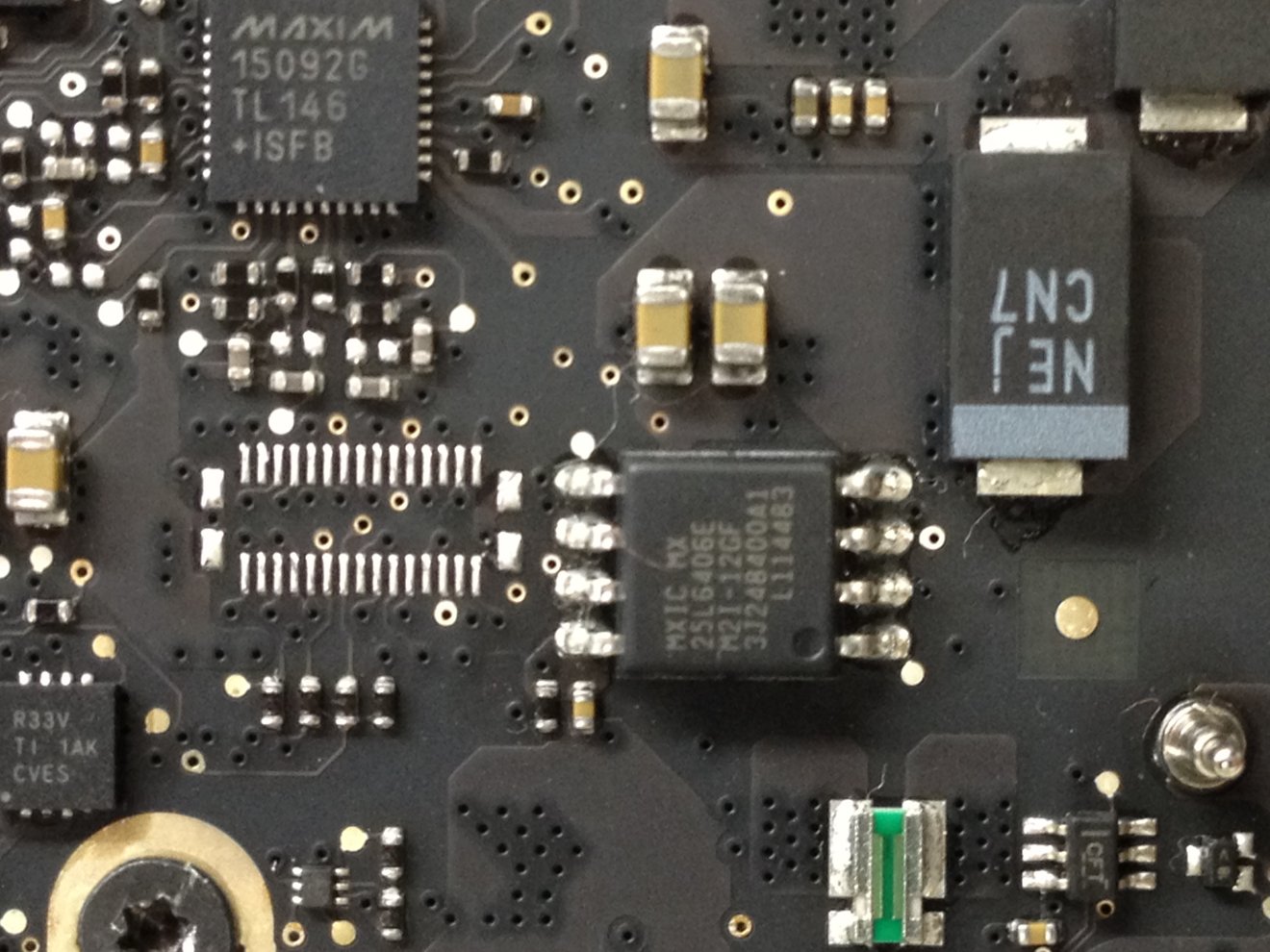








 Andrew O'Hara
Andrew O'Hara
 Amber Neely
Amber Neely
 Sponsored Content
Sponsored Content
 Charles Martin
Charles Martin
 Christine McKee
Christine McKee
 Malcolm Owen
Malcolm Owen











22 Comments
I'm glad these guys are finding these strange little back doors so Apple can lock them up with future updates. I'm not too worried about this one since it requires physical access.
Come on APPLE! This was discovered in 2012 and you haven't fixed it YET???
1) Chance of being an issue are pretty virtually nonexistent but nonetheless this is still a major vulnerability. 2) I'm curious how a drive with an EFI bootkit that is installed after the drive was encrypted. 3) I assume that disabling your TB ports in System Preferences » Network is far too high a layer to be of any help here.
I sure hope he informed Apple of this before going public.
This is a thunderbolt ROM issue, which I believe is something Apple buys and doesn't code themselves. It's like the USB issue. Apple can't fix that issue either. Intel is responsible for fixing both and they haven't.