Safari, Chrome, Firefox, and Internet Explorer were all successfully exploited during the second day of the annual Pwn2Own hacking contest in Vancouver.
South Korean security researcher Jung Hoon Lee toppled Safari with a use-after-free vulnerability, according to Threatpost. Lee was then able to bypass Safari's sandbox thanks to an uninitialized stack pointer, with the combined exploits netting him some $50,000 in prize money.
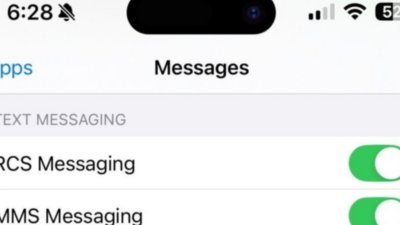
It seems likely that Lee's use-after-free attack was the catalyst for Tuesday's release of Safari 8.0.4, 7.1.4, and 6.2.4, which brought security fixes to the browser on Yosemite, Mavericks, and Mountain Lion, though that has not been confirmed. Apple said that the updates addressed "multiple memory corruption issues" in WebKit.
Meanwhile, Chrome fell thanks to a buffer overflow condition, Firefox went down after an out-of-bounds read/write vulnerability, and a time-of-check to time-of-use flaw took Internet Explorer out.
The Pwn2Own contest is held every year in conjunction with CanSecWest, an annual information security conference in Vancouver. Researchers often use the venue to disclose new exploits, which are developed for months in advance.
During Pwn2Own, contestants have 30 minutes to exploit browsers using remote code execution. The exploits must run without any input from the user apart from browsing to a maliciously-crafted website.
Successful hacks earn their creators prize money, with those that involve substantial privilege escalation earning even more. Lee won a total of $225,000 in prizes during the two-day competition.
 AppleInsider Staff
AppleInsider Staff







 Charles Martin
Charles Martin
 Wesley Hilliard
Wesley Hilliard
 Marko Zivkovic
Marko Zivkovic
 Malcolm Owen
Malcolm Owen

 Andrew Orr
Andrew Orr

 Christine McKee
Christine McKee






19 Comments
Safari, Chrome, Firefox, and Internet Explorer were all successfully exploited during the second day of the annual Pwn2Own hacking contest in Vancouver.
South Korean security researcher Jung Hoon Lee toppled Safari with a use-after-free vulnerability, according to Threatpost. Lee was then able to bypass Safari's sandbox thanks to an uninitialized stack pointer, with the combined exploits netting him some $50,000 in prize money.
It seems likely that Lee's use-after-free attack was the catalyst for Tuesday's release of Safari 8.0.4, 7.1.4, and 6.2.4, which brought security fixes to the browser on Yosemite, Mavericks, and Mountain Lion, though that has not been confirmed. Apple said that the updates addressed "multiple memory corruption issues" in WebKit.
Meanwhile, Chrome fell thanks to a buffer overflow condition, Firefox went down after an out-of-bounds read/write vulnerability, and a time-of-check to time-of-use flaw took Internet Explorer out.
The Pwn2Own contest is held every year in conjunction with CanSecWest, an annual information security conference in Vancouver. Researchers often use the venue to disclose new exploits, which are developed for months in advance.
During Pwn2Own, contestants have 30 minutes to exploit browsers using remote code execution. The exploits must run without any input from the user apart from browsing to a maliciously-crafted website.
Successful hacks earn their creators prize money, with those that involve substantial privilege escalation earning even more. Lee won a total of $225,000 in prizes during the two-day competition.
The funny thing is that those exploits could have been found by others, and used for months. WouldnT be better to have an incentive for them to disclose as fast as possible and receive the prize then. Though, Apple releasing now means its probable they knew in advance.
It's clear that I'm in the wrong business. While I'm sure that his exploits were learned after many weeks or months of hard work and possibly with team help, $225,000 is far beyond what I earn in a few years. During my work I run across exploits or bugs in company software by barely even trying!
... Lee won a total of $225,000 in prizes during the two-day competition.
Quarter-mill for two days? I'm thinking of going from software development to security-exploits. There's certainly more money in this. That being said, it's money well spent if it means it squashes more security bugs.
The funny thing is that those exploits could have been found by others, and used for months. WouldnT be better to have an incentive for them to disclose as fast as possible and receive the prize then. Though, Apple releasing now means its probable they knew in advance.
Must you quote the entire article?
Lee won a total of $225,000 in prizes during the two-day competition.
Let's see...how many ?Watch Edition's is that???