OS X El Capitan, launched earlier on Wednesday, still contains serious vulnerabilities in its Gatekeeper and Keychain features, according to security researchers.
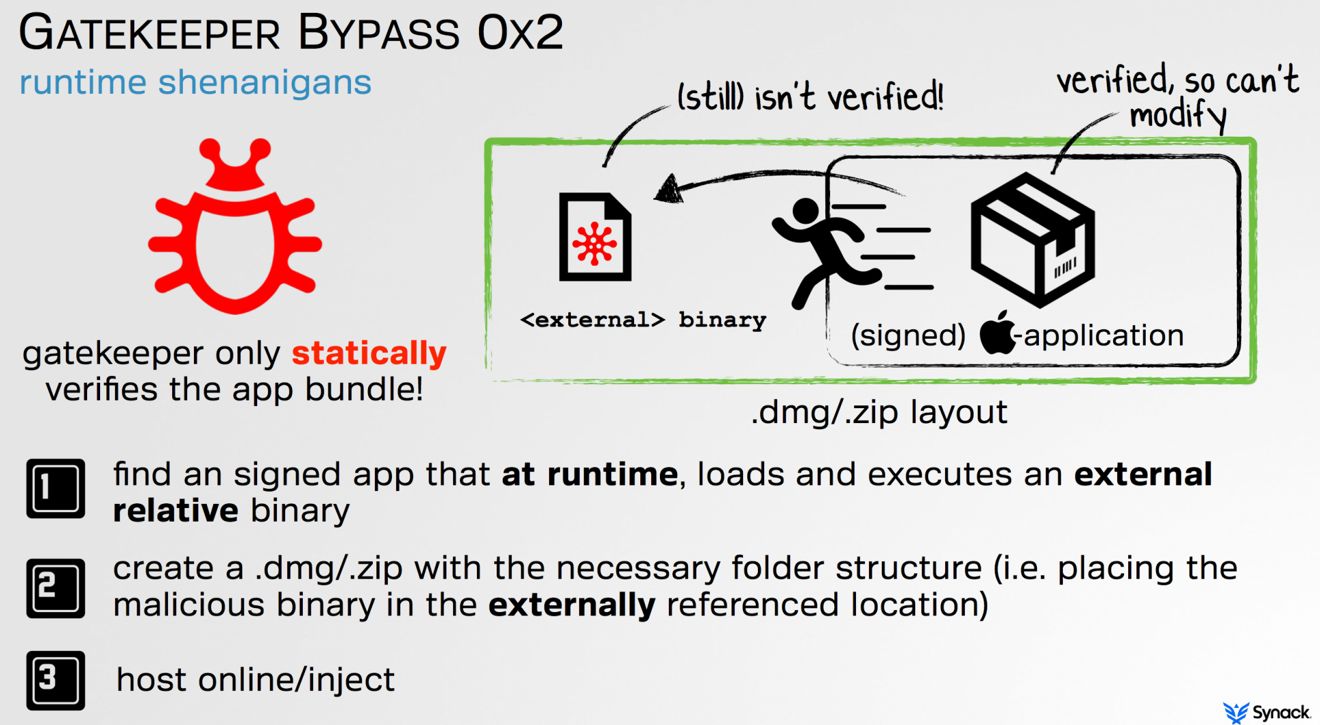
When scanning app bundles, Gatekeeper does a single check and fails to continue scanning after the bundle is actually opened, Synack researcher Patrick Wardle said to Forbes. In a proof-of-concept experiment Wardle bundled unsigned malware alongside an Apple-signed terminal app, and Gatekeeper left the malware unchecked.
Wardle refused to name the Apple-signed app, claiming that might put Mac owners at risk, but noted that it launched the second app in its own directory, and then stopped running. Though his technique opened up a terminal, he was able to render it invisible simply by renaming the correct app.
Apple was reportedly informed about the Gatekeeper flaw earlier this year, and even had it demonstrated to a security team. Wardle suggested to Forbes that Apple could fix the hole by blocking hidden files, or at least offering users a warning about them. The company could be holding back because this approach might break some legitimate apps.
The OS X Keychain vulnerability has been known by Apple since Oct. 2014, and involves "poisoning" the Keychain via an unauthorized app — in turn allowing a hacker to steal or delete sensitive data, Forbes noted. Researcher Luyi Xing, from Indiana University Bloomington, said that Apple informed his group a solution would involve a major overhaul of Keychain's infrastructure.
In the meantime, an open-source app called XGuardian can be used to protect a Mac, Xing said.
El Capitan is focused mainly on improving features like Spotlight and Safari, as well as boosting performance. Its first maintenance update, OS X 10.11.1, is already in beta, but whether it will tackle Gatekeeper or Keychain is unknown.