Saying that whatever method was used by the FBI will have a "short shelf life," Apple on Friday revealed it has no intention to sue the bureau in an effort to find out how it hacked the iPhone 5c used by a terrorist in California.
Comments on the case were given on background, without names, by Apple attorneys in a conference call with members of the media. Officials apparently said they are confident that the method used by the FBI will not be a security concern for most users, according to ZDNet.
Apple's attorneys said they did not know what method the FBI used to crack the iPhone 5c at the center of the San Bernardino terror investigation, but said that normal product development would eventually address whatever exploit was used.
FBI director James Comey revealed on Thursday that the hack used won't unlock anything newer than the iPhone 5c. Beginning with the iPhone 5s and Touch ID, Apple began implementing a secure hardware enclave that makes it much more difficult to crack into a passcode-locked iOS device.
"This doesn't work on 6S, doesn't work on a 5S, and so we have a tool that works on a narrow slice of phones," Comey said.
Comey was also noncommittal as to whether the FBI would tell Apple about the method it used, but he expressed reluctance to lose what little access the bureau does have to locked iPhones.
"We tell Apple, then they're going to fix it, then we're back where we started from," he said. "We may end up there, we just haven't decided yet."
Since the FBI revealed its success late last month, most speculation regarding their method has centered around the so-called "IP Box" that first appeared last spring. That tool — which retails for less than $300 — latches onto a susceptible iPhone's power circuitry and enters PINs over USB.
When a wrong guess is detected, the tool aggressively cuts power to the iPhone's logic board before the guess is recorded, defeating the 10-try limit.
Apple is believed to have patched this hole in older iPhones with iOS 8.1.1; as the iPhone 5c in question is thought to be running iOS 9, the FBI has either chosen a different method or has purchased the device from a company that has discovered an as-yet unreported flaw in later software.
Beginning with the iPhone 5S, PIN guesses are managed in the hardware Secure Enclave, rendering such an attack useless.
Apple's decision not to sue the FBI, and the FBI's decision to drop its complaint against Apple in the San Bernardino case suggest the issue is dying down between both sides — Â for now. But the encryption debate remains contentious between Apple the FBI's parent agency, the U.S. Department of Justice, which revealed on Friday it plans to continue pushing to force Apple to unlock an iPhone 5s at the center of a Brooklyn drug trafficking case.
 Neil Hughes
Neil Hughes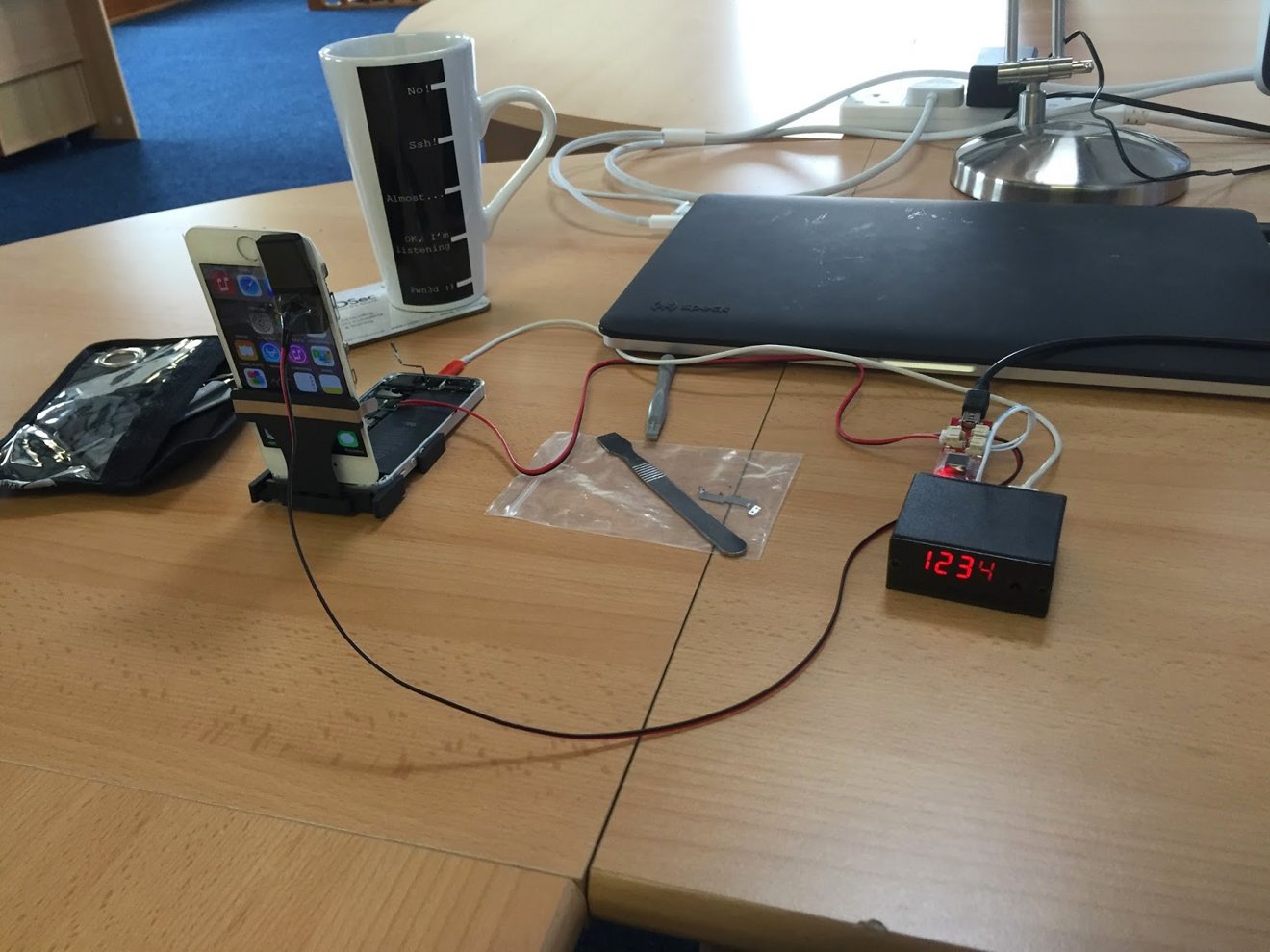








-m.jpg)





 Wesley Hilliard
Wesley Hilliard
 Malcolm Owen
Malcolm Owen
 Andrew Orr
Andrew Orr
 William Gallagher
William Gallagher
 Sponsored Content
Sponsored Content
 Christine McKee
Christine McKee

 Thomas Sibilly
Thomas Sibilly






16 Comments
Ala the "FAA Passenger Ban" article from the Onion, the iPhone 8 should contain just the box--opening it up reveals...nothing (just the instructions. Oh, and SIM Removal Tool--to help out friends with "insecure" iPhones)!
This would be 100% effective against hacks. Guaranteed.
This narrative goes against the one in the news today that Apple will work to find out what the hack was as part of the drug case in NY. They are said to push for the details as to understand what the FBI has done to try and get into the iPhone 5s they have in custody.
Because they probably already know, that's why they made the 5s.
It's obvious what the FBI did.
They went around the counter by copying out the memory, rebooting, trying a few time, copying in the saved memory,, rebooting, trying again,, etc... Until they got in.
It's possible because the retry counter is in main memory; with the 5s, that's no longer the case, the counter is in the secure enclave.
That only really work if you have a short numeric pin.
If they had a long alpha passcode, they could have done that for a decade.
The reason people don't use long pass code is because they're a bitch to type, well on the 5s, 6 and 6s, you don't have to most time because of touch ID, so you can make your pass code very long. That's another reason why the 5s is safer.
Given the speed with which the courts move...
If I had a suspicious nature, I might conclude that Apple agreed to open the IPhone in return for the FBI claiming they had help from a mysterious third party whose name shall not be spoken. But that's just silly. Isn't it?