New router attack altering DNS settings, stealing ad traffic from infected users
Last updated
A second wide-spread attack on vulnerable home networking equipment is underway, with the latest attack redirecting an afflicted network's traffic, including that from Apple users, to fraudulent domains and opening up the routers to further attack.
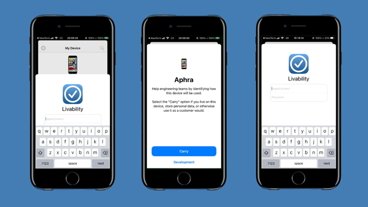
The "DNSChanger" attack vector hides malicious code intended to assault routers in specifically crafted images. The code inside redirects viewers to webpages hosting router-infecting malware itself. The webpages then attack routers running out of date firmware or ones that are secured with weak, default administrative passwords.
"Once compromised, these devices can affect the security of every device on the network, opening them up to further attacks, pop-ups, malvertising, et cetera," security firm Proofpoint's Director of Threat Intelligence Patrick Wheeler told Ars Technica. "The potential footprint of this kind of attack is high and the potential impact is significant."
Pages serving the first stage of the DNSChanger exploit check a user's IP address. Should the user fall in the targeted range, the attack continues. After the target is identified by the first phase of the malware, an image is then served to the victim designed to impact that particular router.
DNSChanger uses the webRTC protocol to launch the attack in the second image. Should the user under attack be utilizing Chrome for Android or Chrome, the attack then identifies the router further, and will alter one of 166 vulnerable router firmwares.
Proofpoint says that it is impossible to list all vulnerable routers, but the D-Link DSL-2740R, Netgear WNDR3400v3 (plus related models), and Netgear R6200 are all subject to attack. At this time, it does not appear that Apple's routers are able to be exploited in such a fashion.
The researchers have discovered that the malicious ads containing the first wave of the attack are being hosted in waves lasting several days at a time through legitimate ad networks and displayed on ordinary, and otherwise safe websites.
After the malware is successfully installed, all devices connected through the router, including Apple ones, are redirected to less legitimate ad agencies — connections generally not secured or authenticated by HTTPS.
At present, ads from Propellerads, Popcash, Taboola, OutBrain, and AdSupply are affected, and re-routing to Fogzy and TrafficBroker.
In addition to redirecting advertising traffic, the assault also attempts to open up remote administration ports on the router, allowing for other attacks. Proofpoint researchers do not believe that this "DNSchanger" attack is directly related to the wide Netgear security vulnerability from Dec. 14, but victims of the latest attack are opened up to the older vector.
"Router vulnerabilities affect not only users on the network but potentially others outside the network if the routers are compromised and used in a botnet," said Proofpoint in a blog post about the attack. "While users must take responsibility for firmware updates, device manufacturers must also make security straightforward and baked in from the outset."
Near the end of November, reports started circulating backed by AppleInsider sources, that Apple may be ending the AirPort family. Former AirPort engineers are now reportedly working on other teams, including Apple TV development.
The internal changes suggest that Apple has no plans to update its existing lineup of routers, including the AirPort Extreme, Time Capsule, and AirPort Express, but do not discount the possibility of the functionality being added to a different product. Apple's AirPort Express network extender and AirPlay audio target has not even been updated to the 802.11ac wi-fi specification.
 Mike Wuerthele
Mike Wuerthele













 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly
 AppleInsider Staff
AppleInsider Staff
 William Gallagher
William Gallagher
 Malcolm Owen
Malcolm Owen
 Christine McKee
Christine McKee









24 Comments
This is one reason I'd like for Apple to continue making routers.
It does make some of the new "smart" routers more attractive since security updates that block just this type of thing (and others) are handled quickly and efficiently. I won't recommend particular names but they're well worth looking into and many are exceptionally easy to set up even for someone who has never done so before.
I'd normally just leave a comment to "use Apple routers" but given the current direction, I'll adjust my messaging: "Do not use Netgear, TP-Link, D-Link, Cisco/Linksys consumer gear. Use router companies that pay attention like Eero, Ubiquiti"