A new malware, dubbed MacStealer, has been found infecting Intel and Apple Silicon Macs, and is stealing passwords, credit card info, and other personal data.
A trio of Windows-based malware families has been uncovered by security researchers Uptycs that take advantage of messaging service Telegram. Now, the team has found a version specific to Mac users.
Referred to as MacStealer, the malware has the ability to take documents, browser cookies, and login information from a target Mac. It also specifically works on Macs running macOS Catalina or later, running on Intel or Apple Silicon chips.
As part of the theft, the software takes credentials and cookies from Firefox, Google Chrome, and Brave browsers, and also extracts the Keychain database. It also attempts to secure a variety of file types, including MP3s, text files, PDFs, PowerPoint files, photographs, and databases.
While pulling Keychain may seem like a big danger to users, the attack involves taking the Keychain wholesale, without accessing the data within it. The database does get taken and transmitted to the attacker by Telegram, but it's still encrypted.
The threat actor selling access to MacStealer for $100 per build says that the extracted Keychain is "almost impossible" to access without the master password. As part of the attempted sale, the actor says they don't "wanna make fake promises" for access to that data, and haven't included it in a list of "upcoming" features.
Other items in the "Upcoming features" list include the draining of cryptowallets, a tool to generate new builds, a reverse shell, a custom uploader, and a control panel.
At the same time as grabbing the files and data, MacStealer then uses Telegram to send over select information to specific channels. A separate ZIP compilation is then shared to a Telegram bot controlled by the hacker.
How to protect yourself from MacStealer
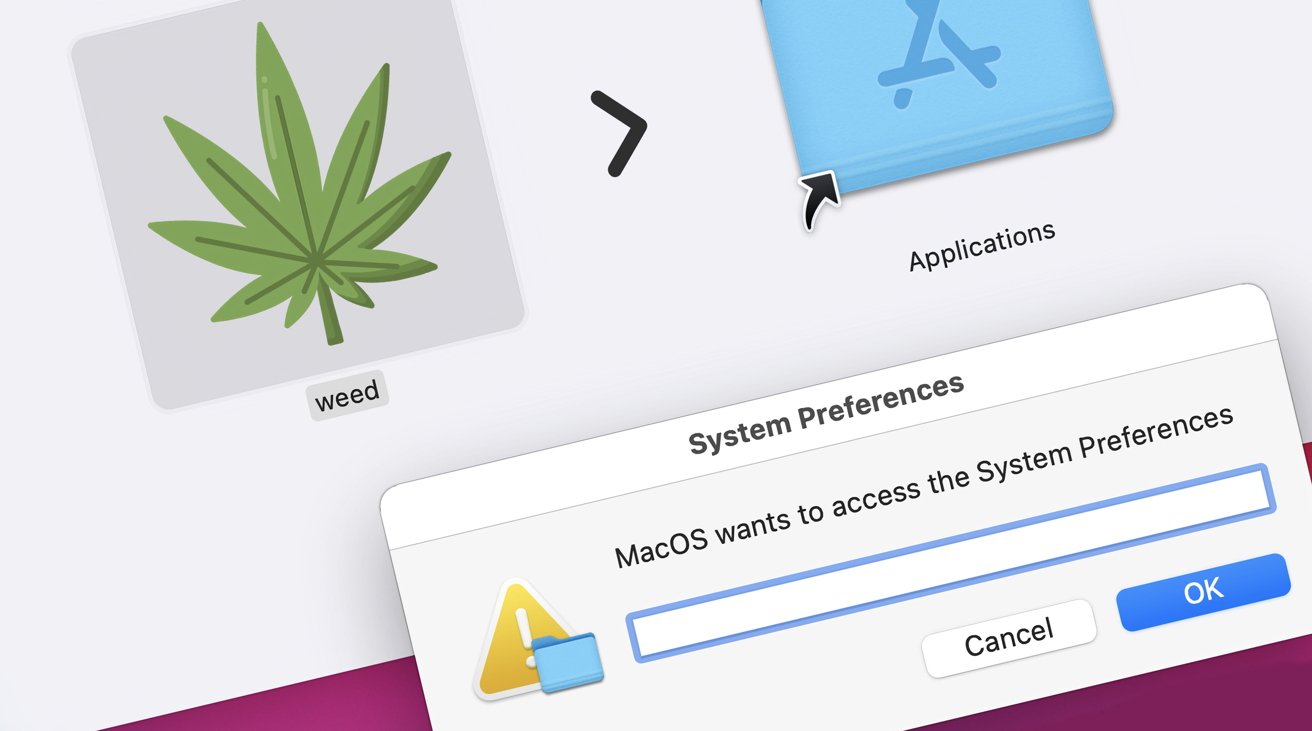
It is unclear exactly how the malware moves between Macs, but initial infections have been caused by an app called "weed.dmg." As you would expect, it looks like an executable with a leaf as an icon.
Attempting to open the file raises a fake macOS password prompt, which the tool then uses to access other files on the system.
The password prompt used by the software is distinctly different from what macOS provides users, so it should be reasonably easy for an experienced Mac user to spot something wrong. A big clue is that it doesn't include an already-populated username field.
Uptycs recommends that users keep their Mac systems up to date with patches and updates. Also, it is suggested to only permit the installation of files from trusted sources, such as the App Store.
![MacStealer's fake macOS password prompt [left], a genuine macOS password prompt [right]](https://photos5.appleinsider.com/gallery/53669-107925-fake-password-real-one-macstealer-xl.jpg)








