Zero-click iOS malware attack through iMessage is actively infecting iPhones
Antivirus provider Kaspersky has discovered a malware campaign explicitly aimed at infecting iPhones running up to iOS 15.7 through iMessage — but it can be found and prevented.
Kaspersky's team identified potentially suspicious behavior emanating from multiple iOS devices. However, due to the security limitations that restrict direct internal examination of iOS devices, the company had to generate offline backups.
These backups were then subjected to analysis using the mvt-ios (Mobile Verification Toolkit for iOS), resulting in the identification of indicators indicating compromise. The attack occurs when the targeted iOS device receives a message through the iMessage platform.
The message includes an attachment that carries an exploit. This exploit, crafted explicitly as a zero-click mechanism, triggers a vulnerability within the system, enabling the execution of malicious code without requiring any user interaction.
After that, the exploit initiates the retrieval of additional phases from the Command and Control (C&C) server. These phases include more exploits specifically devised for elevating privileges.
Once the exploitation process proves successful, a comprehensive APT (Advanced Persistent Threat) platform is downloaded from the C&C server, establishing absolute control over the device and the user's data. The attack eradicates the initial message and exploit attachment to maintain its covert nature.
Interestingly, the malicious toolkit isn't persistent, indicating that the limitations of the iOS environment may be a constraining factor. However, the devices could be reinfected upon rebooting by another attack.
Furthermore, Kaspersky indicated that the attack has effectively impacted devices running iOS versions up to 15.7 as of June 2023. Nevertheless, it remains uncertain whether the campaign exploits a zero-day vulnerability just discovered within older versions of iOS.
The full extent and magnitude of the attack vector are still under investigation.
How to protect yourself
Kaspersky's team is conducting an ongoing investigation into the ultimate payload of the malware, which operates with root privileges. This malicious software possesses the capability to gather both system and user data, as well as execute arbitrary code that is downloaded as plugin modules from the C&C server.
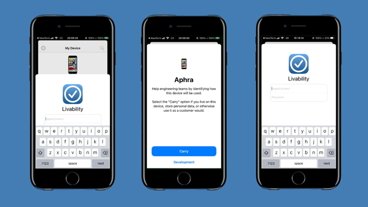
However, they say it's possible to identify if a device has been compromised reliably. Moreover, when a new device is set up by migrating user data from a previous device, the iTunes backup of that device will retain traces of compromise that occurred on both devices, complete with accurate timestamps.
Kaspersky's blog post provides comprehensive guidelines on determining whether your iOS device is infected with the malware. The process entails utilizing the Terminal command line application to install software and inspecting specific files for signs of malware presence.
- Create a backup with idevicebackup2 with the command "idevicebackup2 backup — full $backup_directory."
- Next, install MVT using the command "pip install mvt."
- After that, users can inspect the backup using the command "mvt-ios check-backup -o $mvt_output_directory $decrypted_backup_directory."
- Finally, check the timeline.csv file for indicators with data usage lines that mention the process named "BackupAgent."
This specific binary is considered deprecated and should not normally be present in the device's usage timeline during regular operation.
It's important to note that these steps require a certain level of technical expertise and should only be attempted by knowledgeable users. Updating to iOS 16 is the best — and easiest — way to protect yourself.
 Andrew Orr
Andrew Orr













 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly
 AppleInsider Staff
AppleInsider Staff
 William Gallagher
William Gallagher
 Malcolm Owen
Malcolm Owen
 Christine McKee
Christine McKee









10 Comments
This is a pretty major threat. They say up to 15.7, however, so even devices that cannot update to iOS 16 should be able to be protected if they stay up to date, as the latest iOS 15 version is 15.7.6. This is a great example as to why it's a good idea to always keep your devices up to date as soon as an update is released, as there are generally important security patches present in each and every one. As an end-user, keeping your software up to date is really the only tool you have against zero click attacks such as this one.
Thank goodness for Kaspersky! Shame on all of you who baselessly denigrated them.
Another example of why you should lock your Apple ID and iCloud (not always the same) accounts with a physical security key. Also a good reason to not use a single account for everything.
This is a prime reason I do not use Apple's Keychain to store passwords for everything.
And keep a physical backup of your files and keep it air gapped.