Nothing kills iMessage bridge because it profoundly violated user privacy & security
Nothing and Sunbird pulled the shockingly insecure iMessage bridge, but only after it was discovered that not only did Sunbird log and retain messages, vCards, and more, but that retained user data could also be downloaded by others.
Nothing Chats was pulled from the Google Play Store on Saturday only a few days after it was introduced. Launched on November 14, suspicions were raised about the app within days, including its seeming lack of encryption, and the sending of login credentials over the internet using plaintext HTTP.
On Saturday, things got worse for the Nothing and Sunbird service, with more revelations over the astounding lack of security safeguards for the app.
Early in the day, Nothing removed the app from the Google Play Store. In a post on X, formerly Twitter, the phone maker somewhat optimistically says it is "delaying the launch until further notice to work with Sunbird to fix several bugs."
Before Nothing pulled the plug, Android app developer Dylan Roussel made some discoveries about the app that demonstrated it as being extremely insecure for its users. In a thread, Roussel declared that Sunbird had "access to every message sent and received through the app on your device," that all documents including images, videos, and vCards sent through the app are publicly viewable, and that Nothing Chats doesn't use end-to-end encryption at all.
Pushed forward by a claim by Sunbird that HTTP was fine for an initial request, Roussel says that Sunbird has access since it abuses error detection tool Sentry. Rather than using it to log errors, Sunbird instead used Sentry to log the messages and pretending they were errors.
After trying and succeeding with texts, Roussel then tried sending other forms of media, and found that they were sent to Firebase. He then wondered if it was possible to see media posted by other users, and not only managed to generate a list, but was able to access some elements.
Sunbird has access to every message sent and received through the app. They do this by abusing @getsentry, which is used to monitor errors.
— Dylan Roussel (@evowizz) November 18, 2023
But Sunbird logs messages, pretending they are errors.
Here are part of the requests (img 1, 3) and their entire "message" (img 2, 4) pic.twitter.com/pzwwQVWfOb
More than 637,000 media items were stored by Sunbird at the time of the thread's posting. That collection included vCards, which the app suggests to send to others at the start of a conversation so that the user's Apple ID email address is merged with a phone number on the contact's phone.
Roussel then proceeded to download one of the 2,300 or so vCards in the archive, proving it was possible to get other users' phone numbers and details.
Files were also stored with the original file names intact. Roussel said this was an issue as it could include part of a URL, or confidential or sensitive information, which has further security implications.
Finally, Roussel said the chats aren't end-to-end encrypted at all. "After discovering that medias are shared publicly, this news comes with the realization that Sunbird, and by extension, Nothing Chats is not end-to-end, as advertised everywhere," the developer wrote.
As for what Nothing could do, at the time Roussel said the app should get removed from the Play Store, and then to warn all users. Under Europe's GDPR, rules, Sunbird has 72 hours from being notified of a vulnerability to notify the victims.
"Nothing Chats was not developed by Nothing. But Nothing should have verified that the app which uses their name is secured, before claiming it is," Roussel comments on the matter. "This is probably the biggest privacy nightmare' I've seen by a phone manufacturer in years."
 Malcolm Owen
Malcolm Owen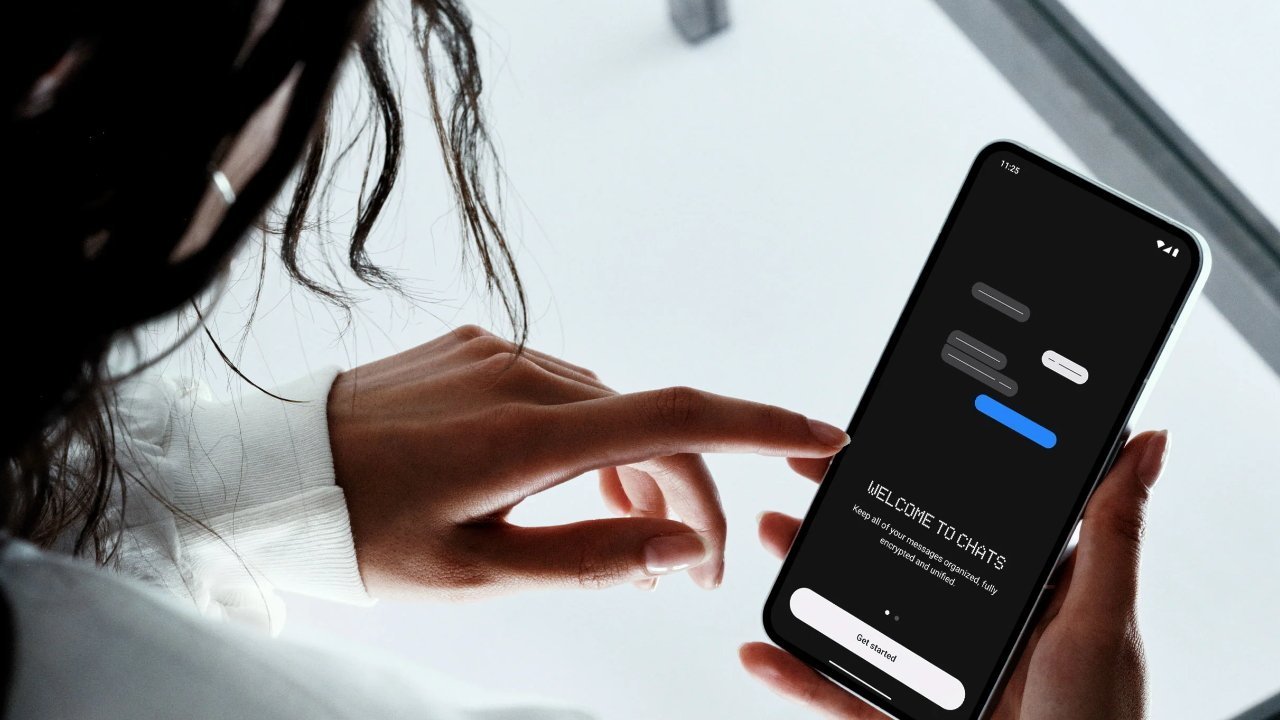













 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly
 AppleInsider Staff
AppleInsider Staff
 William Gallagher
William Gallagher

 Christine McKee
Christine McKee









22 Comments
LOL The fact that it took this long to come to this conclusion is good enough reason for me to expect great things from Nothing.
With any luck, Sunbird will be forced out of business by victim legal actions.
Wow. Nothing's incompetence exposed Sunbird's maliciousness.
This is plain evil in this day and age.
You can really only figure that your iMessage is encrypted when communicating with another iPhone anyway. But now that users are allowing apps. to read. the messages, that all goes out the door. Apple looking to use universal encryption for RCS is just as dangerous and Apple should really. undertake that task themselves. It becomes a bit of a snowball issue though. because they then have to keep up with the Android problems. sheesh.
This either proves that doing this stuff right isn’t easy, or that doing it wrong is. Either way it’s a very good reason to stay with Apple.