Just days after patching the DYLD_PRINT_TO_FILE vulnerability with a new OS X point release, Apple's desktop operating system has been hit with yet another zero-day exploit that would allow an attacker to gain root access without using a password.
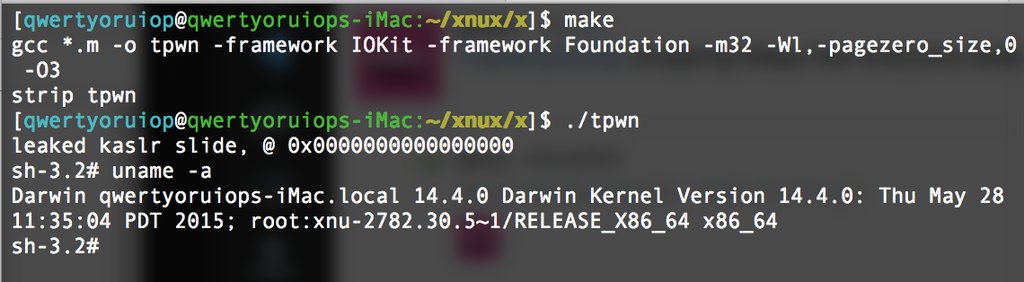
The exploit was discovered by Italian developer Luca Todesco, who relies on a combination of attacks — Â including a null pointer dereference in OS X's IOKit — Â to drop a proof-of-concept payload into a root shell. It affects every version of OS X Yosemite, but seems to have been mitigated in OS X El Capitan, which is nearing release.
Todesco did not disclose the problem to Apple before sharing it publicly early Sunday, so it remains to be seen how quickly the company will respond.
Many computer security researchers condemn such reckless action, arguing that companies should be given time to issue patches for bugs that could harm consumers, while others have become frustrated at the slow pace of response. Apple has a somewhat checkered past with OS X security updates, but has shown improvement in recent months — Â the company patched the DYLD vulnerability less than a month after disclosure.
Apple has also taken steps to harden its operating system against attacks, announcing that OS X El Capitan would ship with a new security feature called "rootless." Rootless is designed to restrict third-party applications from modifying certain parts of the system — even if they are running as root — Â in a manner similar to the more aggressive sandboxing in iOS.