Users can optionally beef up iCloud security, but iCloud Mail, Contacts, and Calendar can't fully use end-to-end encryption. Here's why.
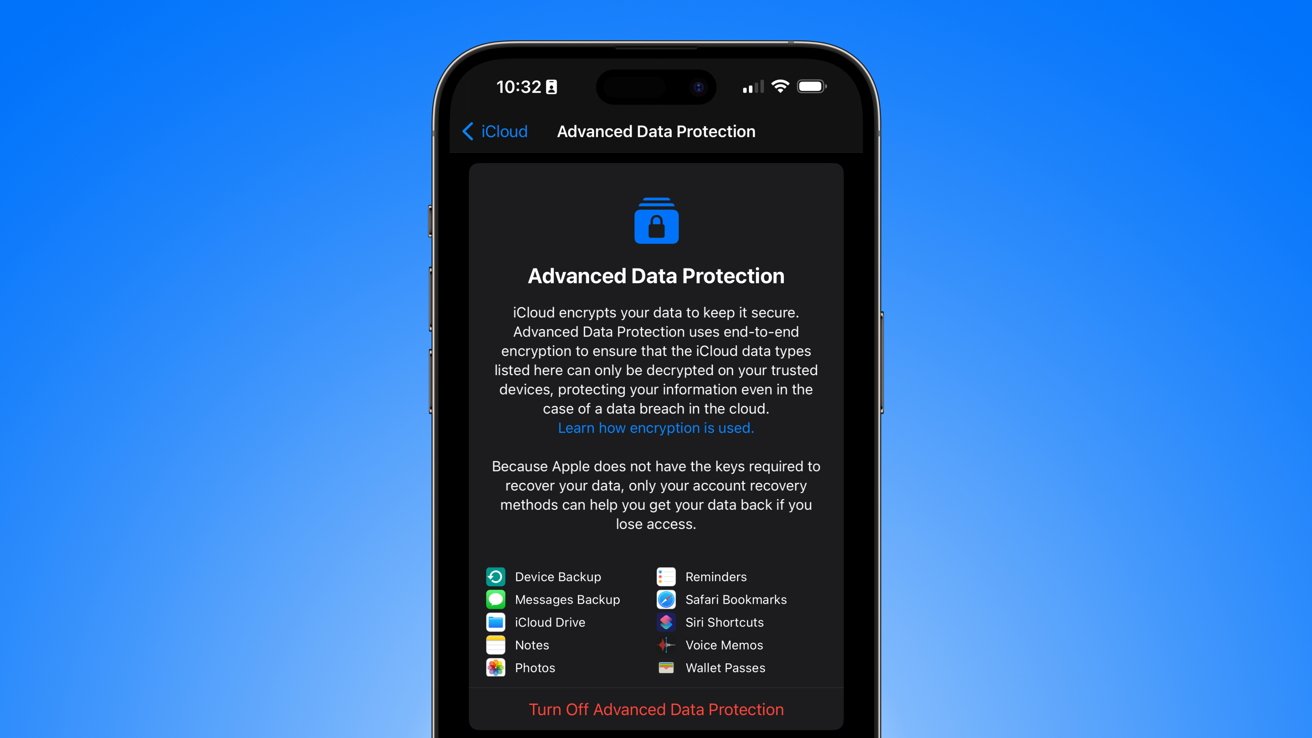
In mid-December 2022, Apple rolled out enhanced security features available to all US-based iCloud users, and referred to as Advanced Data Protection (ADP). Most user data stored on iCloud, and in transit to and from iCloud, is already encrypted as part of Apple's Standard Data Protection practices.
However, in certain circumstances — mostly involving subpoenas from law enforcement or government agencies, or the death of the user — Apple has the encryption keys necessary to make that information available to authorities or legacy contacts of the user. ADP offers users the option of putting custody of some of the decryption keys in the hands of the a user directly, meaning Apple will no longer have that power.
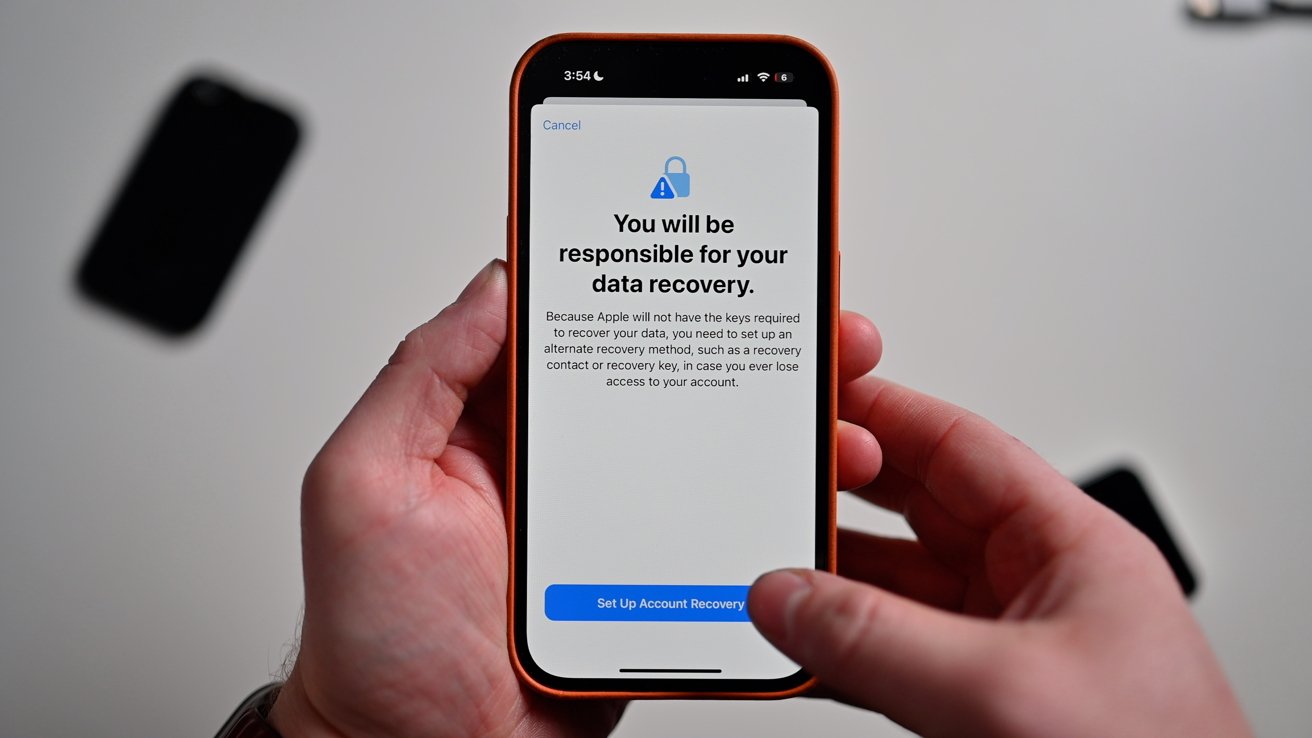
This change means that Apple may be unable to supply some kinds of information stored in iCloud, even under court order. However, turning on this feature also puts responsibility for the decryption keys on the user — Apple cannot assist if a user loses access to their iCloud account, since it would no longer have those keys if ADP is turned on.
What's already encrypted for all iCloud users now
Advanced Data Protection is optional by default, but Apple already protects a lot of user data both in transit and when stored in iCloud under its current policy, now called Standard Data Protection. This means Apple uses end-to-end encryption (E2EE) for health data, payment data, contacts/calendars/reminders, Notes, iMessage and FaceTime content, iCloud Keychain information such as passwords, Home app data, Wi-Fi and cellular interactions and other data with iCloud both in transit and on Apple's servers.
However, Apple has the keys to decrypt some (not all) of this information if subpoenaed or if a legacy contact requests access to the account after a user dies. For example, it can provide a court with a timeline of when iMessages to a certain person were sent, but not the content of them.
Regular SMS text messages, however, are not encrypted as part of the standard. It is also worth noting that if a user employs iCloud Backups for their mobile devices, the encryption key for Messages is contained in the backup.
What's not encrypted, even with ADP turned on
Because of the increased risk of losing data if access to the iCloud account is unrecoverable, ADP should be regarded by most users the same way Lockdown Mode is for Apple devices. If you are a high-value target for snooping, then you will want to consider employing these enhanced-privacy measures — but most users should consider the potential risk before switching them on.
According to Apple, even when ADP is turned on, there are still some features that can be stored encrypted, but with Apple still holding the decryption keys. Specifically, these are iCloud Mail, Contacts, and Calendars.
The reason, according to Apple, is because these apps and features specifically have to interact with outside and third-party email, calendaring, and contact applications. For users to be able to add their iCloud email, contacts, and calendars to — for example — Microsoft's Outlook, or some other third-party email/contacts/calendar app, the information needs to be in a form that can be understood.
Likewise, checksum data used for such things as de-duplication searches, updating file creation and modification dates, and optimizing databases of information like photos are also readable by the system — even if the photos and files themselves are encrypted. This technique is known as convergent encryption, and has always been a part of iCloud.
In these specific areas, Apple's policy is that the metadata is always encrypted, but Apple keeps custody of the decryption keys for compatibility reasons, even if ADP is turned on. The company says it plans to continue to expand ADP to other areas over time, such as in future features — and perhaps expanding it to additional countries, where possible.