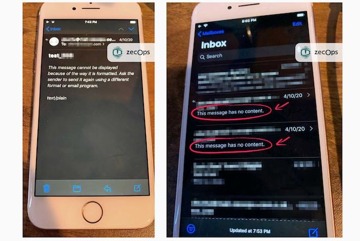
Security researchers have discovered a pair of zero-day vulnerabilities in the Mail app for iPhone and iPad that they have found in the wild, and being used by attackers.
San Francisco-based cybersecurity firm ZecOps said that they came across the two flaws in the default iOS and iPadOS Mail app while running routine digital forensics on customer devices. After further investigation, they found evidence of targeted attacks, which they outlined in a report on Wednesday.
The vulnerabilities allow an attacker to run remote code by exploiting Apple's MobileMail and Mailid processes in iOS 12 and iOS 13, respectively, through the use of a specially crafted email. And, if triggered properly, a user wouldn't know that they were being hacked.
Variants of the flaw stretch back to at least iOS 6, the researchers said. Because the vulnerabilities were used to attack users before Apple could issue a patch, they're considered zero-day attacks, which is significant because iOS zero-days are extremely rare and often quite expensive.
By themselves, the flaws don't pose too much of a risk to users — they only allow an attacker to leak, modify or delete emails. But combined with another kernel attack, such as the unpatchable Checkm8 exploit, the vulnerabilities could allow a bad actor root access to a specifically targeted device.
At least one of the flaws can be triggered remotely without any user interaction — an attack known as a "zero-click." ZecOps added that the second vulnerability was likely discovered by accident while attempting to leverage the zero-click. The vulnerability impacting iOS 13 is the zero-click. While the iOS 12 flaw does require users to actually tap on an email, that requirement doesn't apply to attackers who send messages from a mail server that they control.
In its report, ZecOps found that a number of its customers were targeted, including employees at a Fortune 500 company in North America, a journalist in Europe and a VIP in Germany. Interestingly, while there was evidence that the flaws were executed on targeted devices, the emails themselves weren't present. That suggests that the attackers deleted the emails to cover their tracks.
The researchers believe that the attackers were working for a nation-state that had purchased the attacks from a third party, adding that at least one "hacker-for-hire" organization was selling exploits that use email as the main vector.
On the other hand, security researchers who spoke to Motherboard said that the flaw was relatively unpolished compared to other hacks, meaning that sophisticated attackers would probably deem it too risky to use against "high value targets."
Still, ZecOps notes that attacks using the exploits are likely to increase in frequency since they're now publicly disclosed. The researchers said bad actors will "attack as many devices as possible," meaning that normal users could end up targeted. That becomes more dangerous if the exploits were leveraged by cybercriminals with access to additional vulnerabilities.
The vulnerabilities only impact the native Mail application, and not third-party apps. To mitigate the attacks, ZecOps recommends that users stop using Mail on iOS and iPadOS until a patch is issued. MacOS is unaffected.
ZecOps said it alerted Apple to the vulnerabilities in February. Both of the flaws have since been patched in the latest beta releases of iOS 13, and a fix is set to arrive in the next publicly available iOS update in iOS and iPadOS 13.4.5