A new study says the iPhone isn't as locked down as it could be for the sake of user convenience — but there are steps that you can take to secure your data.
Most important data today is encrypted at rest and end-to-end encrypted when being transferred, like with Apple's iMessage. This means most bad actors cannot get to your most precious data without first unlocking your device.
This system prevents all but the most serious criminals and nation states from accessing your data, but there are flaws. Once a criminal has access to a flaw it can be exploited to gain access to sensitive data. Not all flaws lead to full-device unlock but rather expose specific datasets within the encrypted device.
A study performed at Johns Hopkins University and examined by Wired describe some of the flaws in Apple's approach. Apple uses an internal hierarchy to decide which data receives which form of encryption.
"On iOS in particular, the infrastructure is in place for this hierarchical encryption that sounds really good," says Maximilian Zinkus, a PhD student at Johns Hopkins. "But I was definitely surprised to see then how much of it is unused."
This means Apple has additional levels of encryption and security that isn't being tapped by the operating system or installed applications. Apple is a consumer brand, however, and may not want a device so locked down a user's data is in danger of being lost forever.
If a user loses their password and other authentication methods, data locked behind encryption becomes useless. It is assumed this is why most iCloud data isn't end-to-end encrypted in Apple's servers. Dropping a phone in a lake and losing everything is one thing, forgetting a password and losing your supposedly safe iCloud data is another.
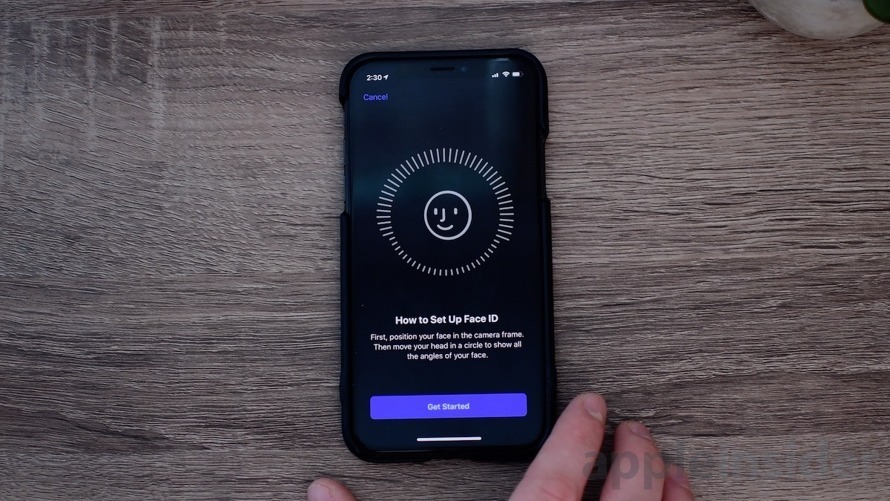
The study focused on a specific set of states a smartphone can be in — Before First Unlock and After First Unlock. If you reboot your iPhone it is in a "complete protection" state that makes it difficult for even advanced forensic tools to access.
The complete protection state is removed after you've entered your password, which is why the state is referred to as After First Unlock. This is your normal mode of encryption with a hierarchical structure to protect specific datasets.
Apple uses something called the Secure Enclave to protect data. It is a physically separate chipset designed to hold security keys in a place not located in the main operating system. You can only access the Secure Enclave After First Unlock and after each biometric or password authentication.
The Secure Enclave protects keys to your most important data like iMessage and Health data. Less protected encryption keys can appear in your quick access memory, which is what forensic tools tend to target. Apple's protections are enough to keep all but the most well-funded criminals out.
"Apple devices are designed with multiple layers of security in order to protect against a wide range of potential threats, and we work constantly to add new protections for our users' data," an Apple spokesperson told Wired. "As customers continue to increase the amount of sensitive information they store on their devices, we will continue to develop additional protections in both hardware and software to protect their data."
The Apple spokesperson said that the methods used in the Johns Hopkins study are very expensive and prohibiting to all but the biggest criminals and governments. The exploits examined also require physical access to the device and stop working as soon as Apple patches them.
The problem is when bad actors want into your device that it has in-hand, it has options. Advanced forensic tools are available from companies like GrayKey or Cellebrite are readily purchased by the United States police forces and public schools.
While these devices are too expensive for the common criminal, they are priced for easy government accessibility. Apple tends to patch vulnerabilities used by these devices fast, but new flaws are found all the time.
What Apple can do
Studies like those conducted at Johns Hopkins are crucial for Apple and other tech companies in the fight for encryption. If anything, this study proves that while iPhone customers are protected from nearly any threat, the government still has access to data when necessary.
Apple is under heavy scrutiny from governments around the world about device encryption. If Apple pushes security further and makes users able to lock down their data more, the scrutiny could get worse, or even drive legislation to end all encryption.
There is a future where Apple can provide more user protections, but not without legal ramifications. Apple has previously been rumored to consider fully encrypting iCloud data, but the FBI apparently dissuaded them. More likely, Apple realized that users could lose their data inadvertently if it is too heavily guarded.
As the Apple spokesperson stated, Apple rides a line between security and convenience. Face ID and Touch ID help keep a device safe while customers benefit from easy access to an encrypted device. The next iPhone could have multiple forms of biometrics for even more security at unlock, but that will still only go so far.
What you can do to further protect data
Of course, the everyday user should not fear a forensic team snatching up their iPhone to examine their latest selfies, but it is healthy to know how to protect yourself.
Emergency SOS mode
First, know about the emergency modes and reboot shortcuts on your device. If you hold down the volume up button and power button at the same time for five seconds, it triggers an emergency lockdown.
This prevents your device from unlocking with biometrics, and gives you the option to shutdown the phone or call 911. If you shutdown the phone, it will be back to Before First Unlock to provide maximum data protection.
This mode is handy for that moment when you might need to hand over your iPhone to a school teacher or an investigator and you feel the need to protect your data. This also helps with police officers who cannot ask for a password but can sometimes legally request biometric unlocks.
Use an alphanumeric passcode
Many forensic tools rely on guessing passcodes on the device using algorithms. The longer your password, the harder it is to crack.
By adding a couple of letters and a special character you'll increase the time it takes to guess the passcode from hours to hundreds of years. You'll still need to remember the password too, however.
Erase all data after 10 failed passcodes
Users should also be aware of a setting that resets the iPhone to factory settings after 10 failed passcode attempts. After a five failed attempts, you'll be blocked by a timer that gets longer and longer until you're waiting a full hour after the ninth attempt. No normal iPhone use will accidentally cause your device to erase all data.
Local backups
If you want to go to the most extreme level of data protection, consider removing sensitive data from iCloud. You can perform a local iCloud backup by connecting your iPhone to your Mac.
Doing this will enable a local encrypted option, which will secure the backup behind a password you choose. Forget the password and the backup is lost forever though.
Continue as normal
Apple is already doing everything it can to thwart bad actors from breaching your data. Your iCloud data is safe too, and can only be accessed when a proper warrant is presented.
Use your iPhone as normal and live your life. The likelihood of an average iPhone user encountering a forensic tool or wealthy criminal seeking what's on your iPhone is slim to none. The protections Apple provides is enough to keep your data safe and will only improve with time.