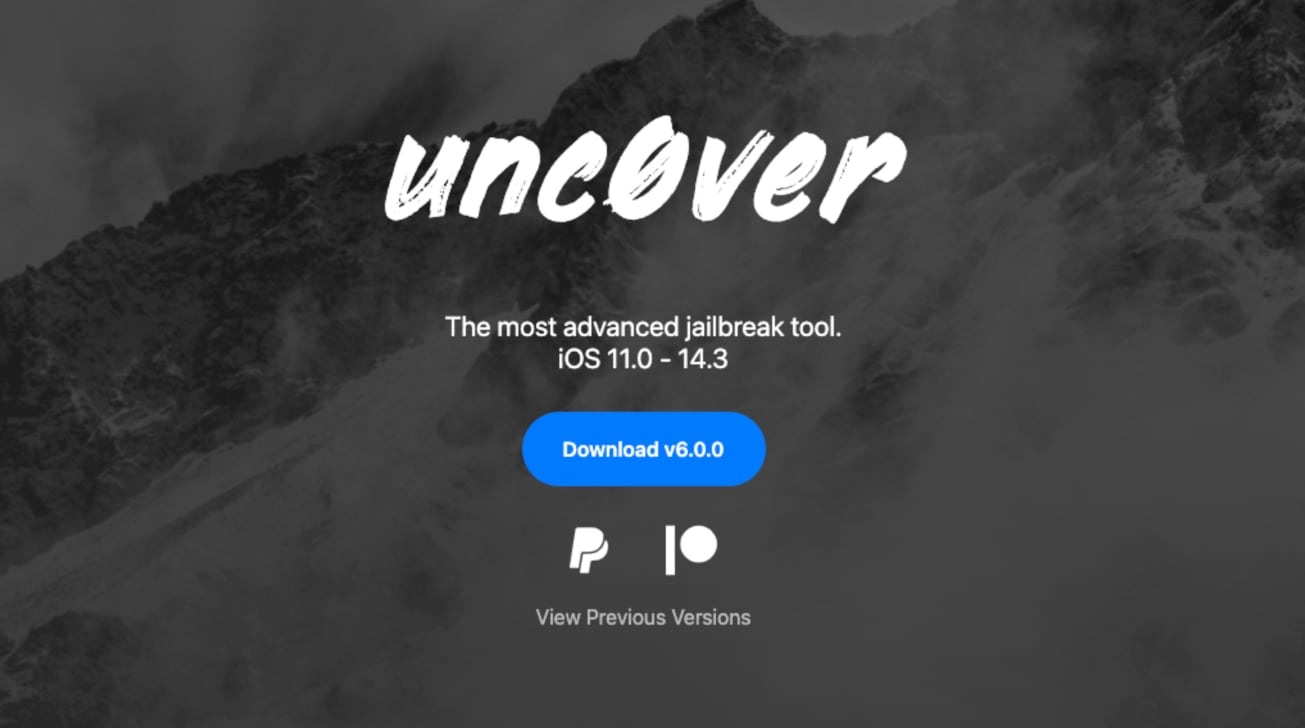
The prominent jailbreaking tool "unc0ver" has been updated to a new milestone release, one that brings support for iOS 14.3 and earlier releases.
The ongoing jailbreak arms race between hackers and Apple has been extended once again, with the jailbreak community gaining an update for the unc0ver tool. Announced by hacker "Pwn2Ownd" via Twitter, version 6.0.0 was released on Sunday to include support for newer releases of iOS.
According to the tool's website, it is able to unlock iPhones running iOS versions between iOS 11 and iOS 14.3. The previous milestone release of 5.0.0 in 2020 brought it up to work with iOS 13.5, while version 5.2.0 in June 2020 furthered the support to include iOS 13.5.5 beta 1.
The tool claims to be "stable" and "secure," by using "native system sandbox exceptions" to retain security while allowing access to related jailbreak files. It has apparently been "extensively tested" to ensure there's a "seamless experience on all devices."
Given that there are three different sets of instructions for performing the jailbreak on macOS, with two involving 14 steps, it isn't a process for the faint of heart.
Numerous mentions to security are made by the tool, in a bid to assure users it is safe to perform. It is also ironic, given that jailbreaking relies on vulnerabilities and flaws in iOS security to work in the first place.
The testing of the tool by its creators ranges from an iPhone 5S up to the iPhone 12 Pro and iPhone 12 Pro Max, along with the iPod touch, iPad Pro, seventh-generation iPad, and iPad mini 5.
While the jailbreak will work with previous releases of iOS, the latest version won't work with the current generation, iOS 14.4. This can always change in the future, if a workaround for Apple's security is discovered, though Apple is already working on iOS 14.5.
Though there is the argument that jailbreaking is beneficial to its proponents, such as getting apps without going through the official App Store, those same users may also be giving up on security. The numerous checks that Apple puts in place for applications in the App Store makes it a very safe digital storefront, and going around it could be a vector for malware to be installed.