AirTag clone developed by researchers works around Apple's anti-stalking measures
Security researchers have created a clone of Apple's AirTag, in a bid to prove to Apple that the device and the tracking protection features of the Find My network can be bypassed.
The AirTag has been the subject of numerous reports involving tracking and personal security, with it being used for thefts and stalking despite Apple including features to limit usage in that way. Following criticism over misuse, Apple said on February 10 it was to introduce several changes to the Find My network to address the stalking issue.
In a blog post published by security researcher Fabian Braunlein of Positive Security on Monday, several "quite obvious bypass ideas" for current and upcoming protection measures were published. Braunlein believes that all can be put into practice.
To test the assumption, a cloned AirTag was produced. The report claims that the stealth AirTag was able to track an iPhone user for over five days, without triggering any tracking notifications.
The researcher came up with ideas to thwart quite a few elements of Apple's planned changes, starting with Apple's claim that every AirTag has a unique serial number that is paired to an Apple ID. The concept doesn't apply here as the clone doesn't use an AirTag serial number, neither for hardware nor in software, and it was not paired with an Apple ID.
While Apple is decreasing the delay before the AirTag beeps from separation from a paired Apple device from over 3 days to between 8 and 24 hours, the clone works around it by not having a functional speaker. Furthermore, this aspect has already been defeated through the sale of AirTags that had their speakers removed or disabled.
On notifications to a potential stalking victim, Braunlein notes that Apple is trading off privacy in two ways. While it wants AirTags to be indistinguishable from others over Bluetooth to prevent identification of a specific tag, Apple also wants to be able to identify specific AirTags over time to determine between tags traveling with the user or one merely passing by.
In Braunlein's example workaround, a list of over 2,000 preloaded public keys was used, with one broadcast by the clone every 30 seconds.
For upcoming changes, items such as privacy warnings during setup, AirPods alert issue changes, and updated support documentation were deemed irrelevant to the clone. Precision Finding using Ultra Wideband is also not covered here, as the microcontroller used didn't include a UWB chip, so cannot be found in that way.
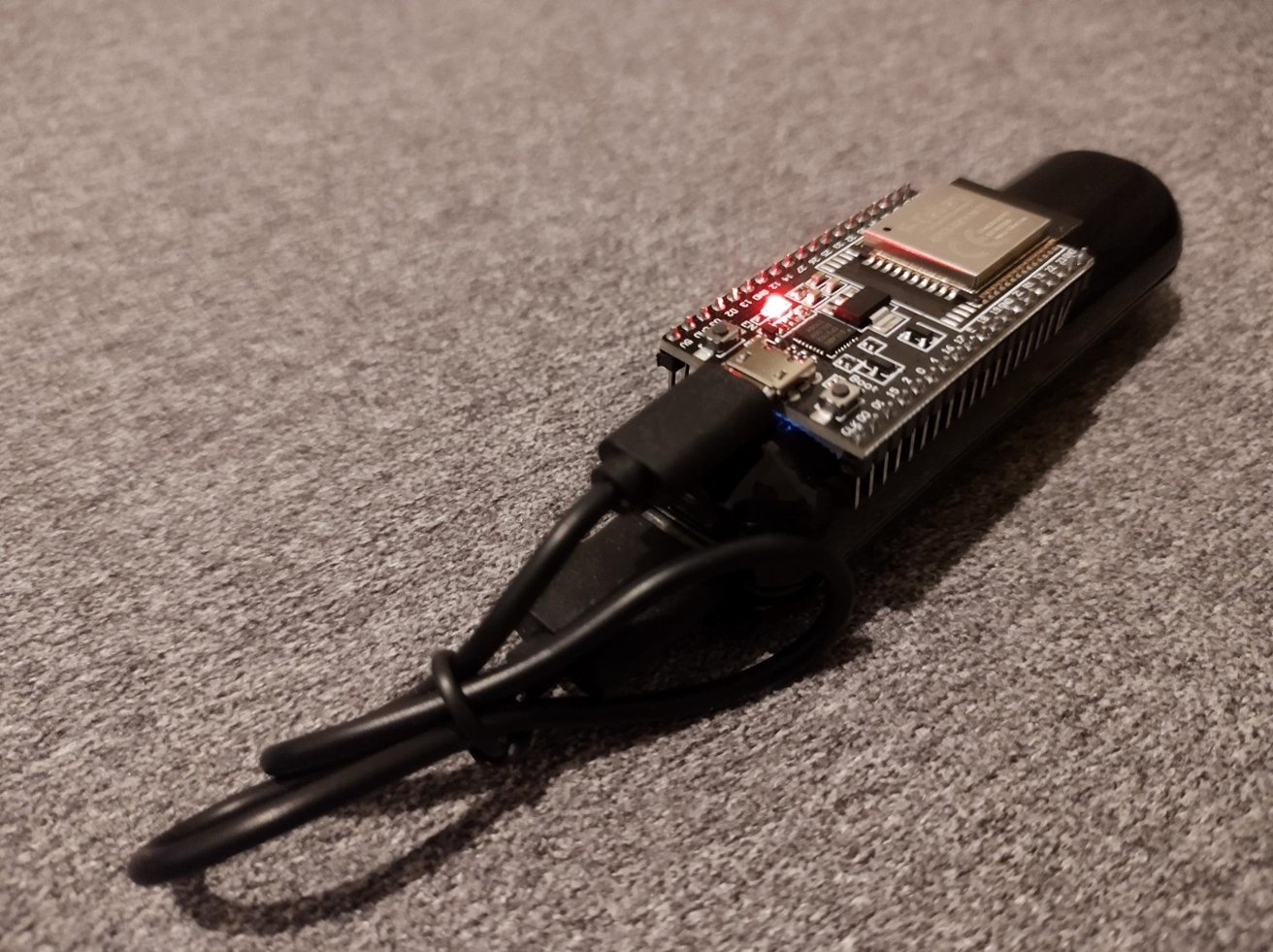
Making the clone
To build the clone itself, Braunlein based the system on OpenHaystack, a framework for tracing Bluetooth devices using the Find My network. Using an ESP32 microcontroller with Bluetooth support, a power bank, and a cable, a non-AirTag clone was created.
The clone used a custom ESP32 firmware that constantly rotated public keys, sending out one periodically, with the list repeated roughly every 17 hours. However, it is thought that a common seed and derivation algorithm used on the clone and a Mac application used to track it could create a "virtually never-repeating stream of keys."
Furthermore, using an irreversible derivation function and overwriting the seed with the next round's output would make it impossible for law enforcement or Apple to get the tag's previously-broadcast public keys, even if they had physical access to the clone.
In testing, the Android Tracker Detect app did not show the cloned AirTag at all. AirGuard, an Android tool that could be used to scan for nearby Find My devices created by the TU Darmstadt lab behind OpenStack, was able to keep track of the cloned device, with it appearing multiple times due to the changing public key.
Over the five days, the clone AirTag was able to be tracked, with the target shown at home and on occasional trips out from the home via a macOS tool modified for the project. Neither the subject nor an iPhone-owning roommate reported receiving any tracking alerts during the period.
A hope for change
In summing up the testing, Braunlein believes the main risk isn't in the AirTags themselves, "but in the introduction of the Find My ecosystem that utilizes the customer's devices to provide this Apple service." Since the current iteration of the Find My network cannot be limited only to AirTags and hardware that officially has permission to use the network, Braunlein thinks Apple should consider shoring up its security.
"They need to take into account the threats of custom-made, potentially malicious beacons that implement the Find My protocol, or AirTags with modified hardware," writes Braunlein. "With a power bank and ESP32 being cheaper than an AirTag, this might be an additional motivation for some to build a clone instead themselves."
The researcher concludes "While we don't encourage misuse, we hope that sharing this experiment will yield positive changes to the security and privacy of the Find My ecosystem."
 Malcolm Owen
Malcolm Owen
![Five days of tracking data produced using the clone AirTag [via Positive Security]](https://photos5.appleinsider.com/gallery/47078-91715-tracked-clone-airtag-xl.jpg)













 Amber Neely
Amber Neely
 Thomas Sibilly
Thomas Sibilly
 AppleInsider Staff
AppleInsider Staff
 William Gallagher
William Gallagher

 Christine McKee
Christine McKee









29 Comments
Researcher or hacker? Makes me wonder whether they’re the same thing.
Apple chose to get into this market. Now that it has, it seems to be leading in protecting Apple and non-Apple customers from potential misuse of AirTags. Clearly there is much more to do. All smartphone and tracking device makers need to protect their customers from misuse of their own and other tracking solutions.
Apple should just stop manufacturing AirTags, and get out of that market entirely. AirTag makes as much sense as the round mouse on the 2001 iMacs.
It is true that airtags have better security than other devices of other brands. Other brands don’t even let people know they’re being stalked. Airtags do. However, people don’t really understand technology to use it correctly, so airtags letting people know they’re being stalked is backfiring as bad marketing for Apple instead. Too much drama.