Families of the victims of last year's San Bernardino massacre plan to file a legal brief in support of U.S. Department of Justice efforts to unlock an iPhone used by one of the shooters, adding weight to the government's case against Apple, a report said Sunday.
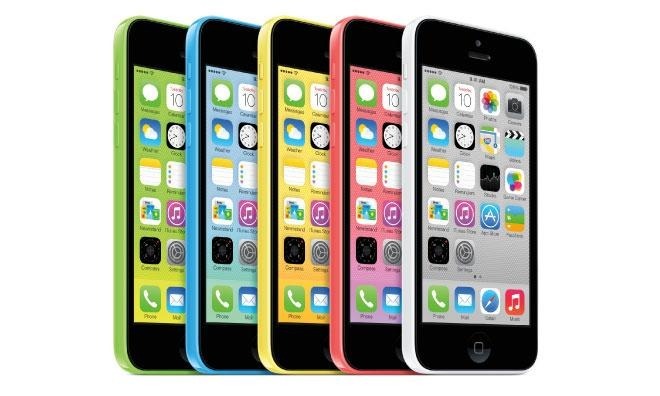
A lawyer representing the victims told Reuters that his clients have a special interest in seeing Syed Rizwan Farook's iPhone 5c unlocked and its data analyzed.
"They were targeted by terrorists, and they need to know why, how this could happen," said Stephen Larson, who served as a federal judge before going private.
Tashfeen Malik, Farook's wife and accomplice in the San Bernardino attack, pledged her loyalty to terrorist group ISIS and its leader Abu Bakr al-Baghdadi on Facebook prior to carrying out the attack. The Islamic State later took responsibility for the shooting that left 14 people dead, not including the couple who died in an ensuing gun battle with law enforcement officers.
FBI and Justice Department officials are seeking information potentially stored on Farook's iPhone 5c, but the device is protected by a passcode. Officials were able to recover iCloud backups saved on Apple's servers, though the most recent data dates back to October 19.
A federal magistrate judge last week ordered Apple to assist in FBI forensic efforts, an action supported by a DOJ motion to compel filed days later.
Apple CEO Tim Cook posted an open letter to Apple's website opposing the request, saying the company has no tools in its arsenal that can break iOS encryption. Further, creating a workaround would fundamentally undermine the security protocols currently being used to protect consumer information stored on hundreds of millions of iOS devices.
"We mourn the loss of life and want justice for all those whose lives were affected," Cook said. "The FBI asked us for help in the days following the attack, and we have worked hard to support the government's efforts to solve this horrible crime. We have no sympathy for terrorists."
It was learned late last week that the FBI purposely called on the iPhone 5c's owner San Bernardino County Department of Health, where Farook worked for five years, to reset the associated Apple ID password hours after impounding the device in December in an attempt to glean on-site data. Apple engineers, who were not made aware of the change until they were consulted January, said the move negated the possibility of extracting data from the handset without also breaking its encryption.
Apple is scheduled to respond to the court order on Feb. 26.