A security company says it blocked a widespread malware campaign that hijacked fake Mac support pages to steal passwords, browser data, and cryptocurrency.
Between June and August 2025, CrowdStrike's Falcon platform detected more than 300 attempts to deliver Shamos, a variant of Atomic Stealer. The operation was run by Cookie Spider, a group that rents out malware to other criminals on a subscription basis.
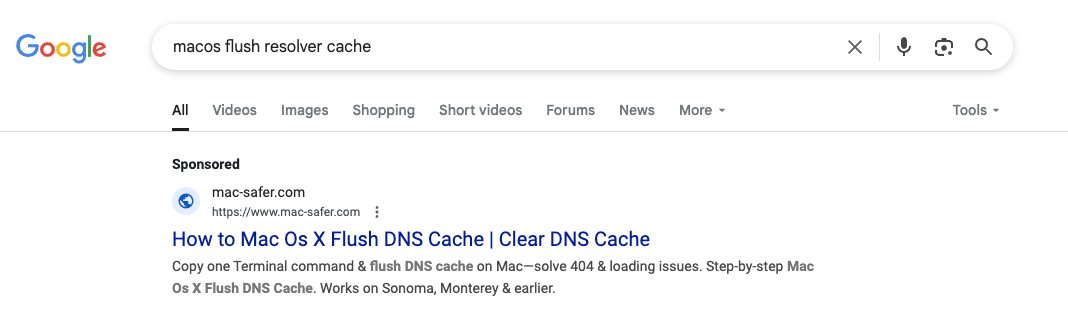
The attackers used malvertising, slipping their fake sites into paid search results. Anyone looking for routine fixes such as how to flush the DNS cache on macOS risked landing on one of the phony support pages.
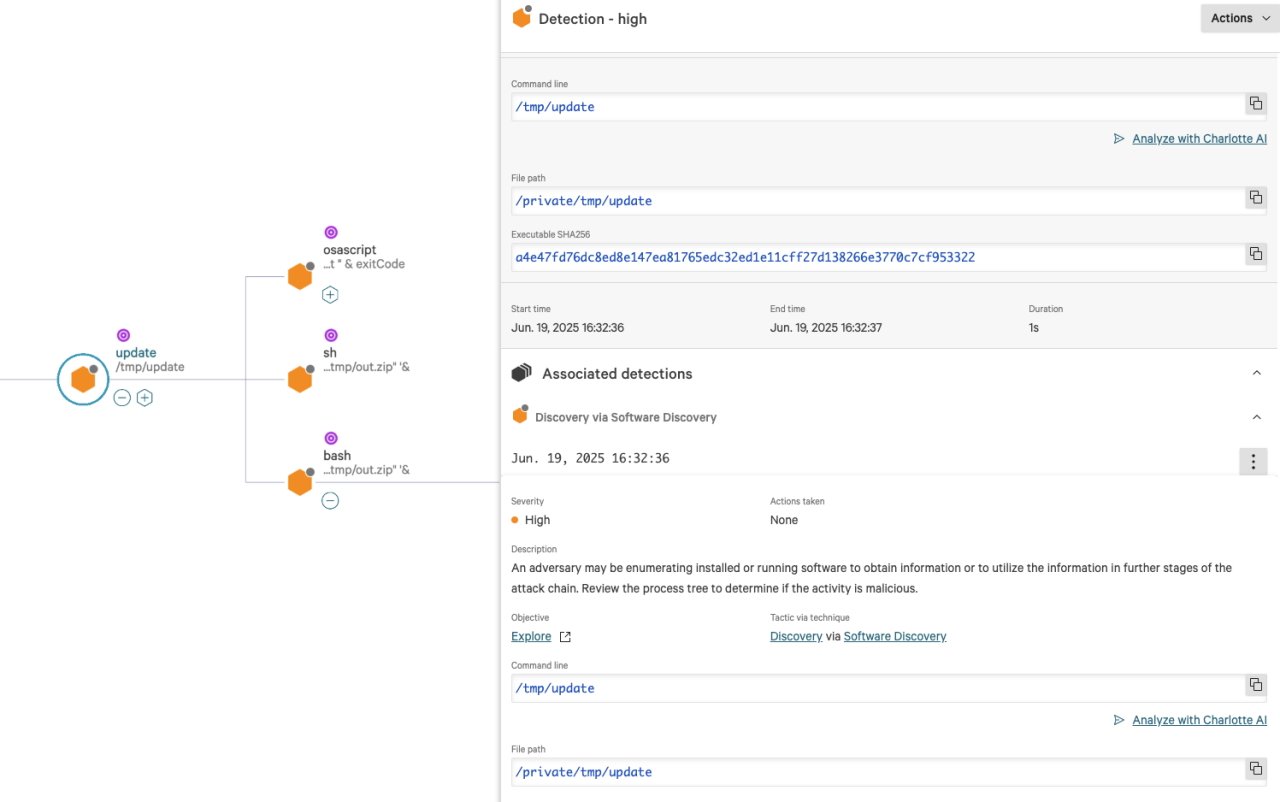
Those pages gave misleading instructions that told users to copy a single command into Terminal. It looked like a quick fix, but the command bypassed Apple's Gatekeeper checks and downloaded a hidden installer.
Sometimes the command was written in plain text. Other times it was disguised with Base64 encoding. Either way, it triggered the same script that grabbed the victim's password, planted the Shamos binary, and set up persistence.
What Shamos steals
Once installed, Shamos searched the Mac for sensitive files, including Apple Keychain entries, browser data, and Notes. It hunted for cryptocurrency wallets as well, which have become a frequent target in modern malware campaigns.
The stolen files were zipped and exfiltrated using the curl utility, a standard macOS command-line tool. Researchers also found the malware pulling down a spoofed Ledger Live app and a botnet module that expanded the attack's reach.
For persistence, Shamos planted a LaunchDaemons entry to ensure it would reload every time the system started. It also ran checks to avoid detection in sandboxed or virtual environments.
Why the scam worked
The success of the campaign hinged on a simple trick. Social engineering was wrapped in technical jargon.
Many Mac users who saw what looked like official instructions likely assumed they were safe. By using search advertising, the attackers did not need to rely on shady emails or torrents.
The criminals also avoided targeting Russia and former Soviet states. Underground forums often ban operators from hitting local users in order to stay out of trouble with law enforcement.
The Falcon platform detected the campaign with a combination of machine learning and behavior-based alerts. According to the company, it stopped Shamos at several points in the attack chain, including the initial download and execution of the shell script.
CrowdStrike also published indicators of compromise, including malicious domains such as mac-safer.com and rescue-mac.com. Security teams were urged to check for any activity tied to those URLs.
What it means for macOS security
Apple has long marketed macOS as a secure environment, but the rise of specialized stealers like Atomic and its variants has weakened that reputation. Gatekeeper, which is designed to block unverified software, was bypassed with a single line of code.
Convenience can work both ways. One-line installers are useful for legitimate tools, but they also make it easy for criminals to sneak in malware. The method has already appeared in several campaigns dating back to 2024.
CrowdStrike expects criminals to continue using malvertising and one-line installation commands. The approach works, and as long as people trust quick fixes from search results, there will be plenty of victims.
How to stay safe
Mac users do not need to panic, but they should be cautious. The safest option is to avoid pasting Terminal commands from unverified websites. For system-level help, Apple's official documentation or established developer forums are far safer resources.
Installing apps only from the Mac App Store or verified developer sites greatly reduces the risk. Keeping macOS updated ensures that known security flaws are patched quickly.
Experts also recommend using endpoint protection software that can catch malicious scripts in real time, including CrowdStrike Falcon and other trusted tools.
Above all, remain skeptical of any website that promises an instant fix to a technical problem. Taking a few extra minutes to verify the source could be the difference between solving an issue and handing over your digital keys.