An Apple patent granted by the U.S. Patent and Trademark Office on Tuesday describes a technique of determining with acceptable accuracy whether an incorrectly entered credential, such as a password, was the result of a mistake or a legitimate threat to a secure network.
While similar systems exist, Apple's U.S. Patent No. 8,412,931 for "Techniques for credential strength analysis via failed intruder access attempts" details a "credential analysis service" that can establish a certain strength of security access in response to a failed access attempt.
Invented with server products, data centers and secure Intranets in mind, the patent can also be used on other platforms as necessary, including wired and wireless networks.
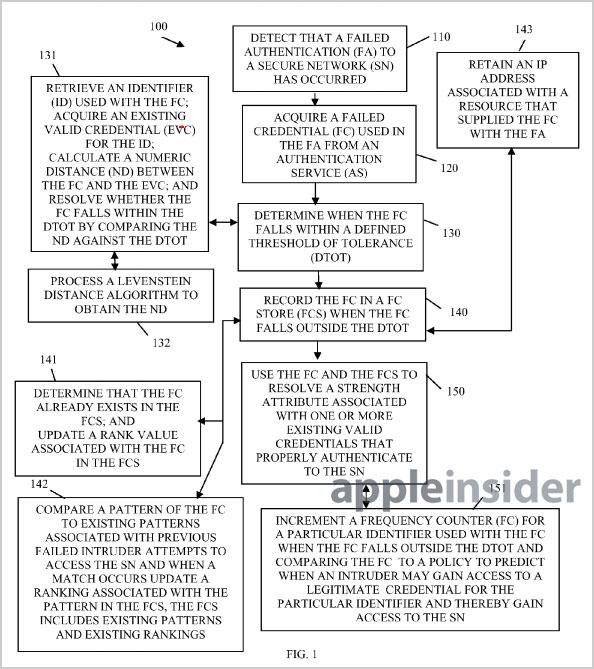
In operation, the credential analysis service is fairly straightforward. As an example, the patent uses an enterprise's secure network, where the system first interacts with a password or security service. Users attempting to access the network require authentications, such as tokens or other means of identification, with a number of roles and levels of security rights.
When an invalid or failed authentication occurs, the system acquires said credential from the authentication service and determines if the invalid login is from a certified user or an intruder. Because users sometimes forget part of their password or enter errant keystrokes, a predefined threshold is employed to help determine if the failed attempt should be processed.
For example,the credential analysis service can retrieve an identifier used with the failed authentication and compare it with an existing valid credential for the identifier. The service then calculates a numeric distance between the two credentials and compares the result with the defined threshold of tolerance. If the number is inside the threshold, no further action is taken, but if the result is outside the tolerated metric, steps are taken to dynamically modify security strength.
One of the steps could be the recording of the failed credential, wherein a counter is employed to track the number of times a certain failed password is used. This recording warrants a heightened ranking for the specific authenticator. In another embodiment, the analysis service compares a pattern associated with the failed attempt with attempted access patterns of known intruders.
In addition to other metrics, the credential analysis service can dynamically change the strength attributes relating to the given credential. An authenticator can be permanently blocked according to some embodiments, or downgraded based on policy.
In still other embodiments, an intruder analysis service that uses many of the same techniques described above determines whether an unauthorized user is attempting to access a network. Intruder trends can be monitored and policy changed based on the findings and historical data as well as patterns.
Apple's credential service patent was first filed for in 2007 and credits Srinivas Vedula and Cameron Craig Morris as its inventors.