Apple's camera and microphone indicators are supposed to tell iPhone users when the microphone or camera are on, but after a device is fully compromised with kernel-level access by another hack, Predator spyware can prevent those from appearing.
Camera and microphone indicators, which first appeared in iOS 14, are a big part of Apple's privacy message. Users depend on them to know when recording is going on.
Security researchers at Jamf found that Predator spyware can prevent those iOS recording indicators from appearing. It's not a standalone attack though — the technique is post-compromise behavior, and the analysis doesn't describe a new iOS vulnerability or a flaw that needs patching.
Predator does this by injecting code into SpringBoard, which manages the status bar and home screen. By intercepting sensor activity updates before they reach the UI, Predator allows the camera or microphone to operate without triggering the familiar green or orange dot.
Otherwise, the iPhone continues to function normally, giving users no obvious reason to suspect surveillance. Apps still launch, notifications arrive, and the interface behaves as expected, but the visual indicator never appears.
A report from Jamf Threat Labs points out that this trust depends on internal system behavior that extremely advanced attackers can tamper with after deep compromise. The discovery raises concerns about how much confidence users should place in UI-level privacy signals when a device is already under an operator's control.
How iOS normally shows recording indicators
On an iPhone, individual apps can't control the recording indicators. When the camera or microphone is in use, iOS sends a notification to SpringBoard, which updates the status bar.
The separation is designed to stop apps from sneaking around and hiding sensor access. Normally, if recording begins, you'll see the indicator pop up.
The research shows that Predator hooks a single SpringBoard method used to handle sensor activity changes. When that method is triggered, the spyware intentionally nulls out the call, causing the message to be quietly discarded.
In Objective-C, messages sent to a "nil" object are silently ignored. Because iOS aggregates camera and microphone activity through the same internal pipeline, one hook suppresses both indicators at once.
SpringBoard never learns that recording began, so no dot is shown.
Why this approach is hard to notice
Earlier spyware techniques often relied on hiding the interface or simulating a powered-off phone. Those methods could raise suspicion when a device behaved inconsistently.
The predator leaves the phone fully operational, so apps launch normally, notifications arrive, and the interface behaves as expected. You might not even notice the absence of an indicator because it's so subtle and easy to miss.
The report doesn't suggest App Store apps can bypass Apple's privacy indicators. Predator operates at a system level and requires deep compromise of iOS, including kernel-level access and code injection into protected processes.
Jamf's analysis also indicates the spyware's stealth is modular rather than automatic. A VoIP recording component lacks built-in indicator suppression, implying operators must activate the indicator-hiding module first before relying on it for covert capture.
Access like this puts the threat in the category of commercial spyware instead of everyday malware. Tools designed for targeted surveillance operate under very different assumptions than typical App Store threats, but for most users, Apple's recording indicators still do their job.
How to protect yourself
Predator needs a full device compromise with kernel-level access, usually through zero-day exploits or very targeted attack chains. For most iPhone users, the concern isn't everyday malware but rather sophisticated surveillance campaigns targeting specific individuals.
Keeping iOS up to date is the first layer of protection. Apple often patches vulnerabilities that spyware operators use, so installing updates quickly reduces the attack surface.
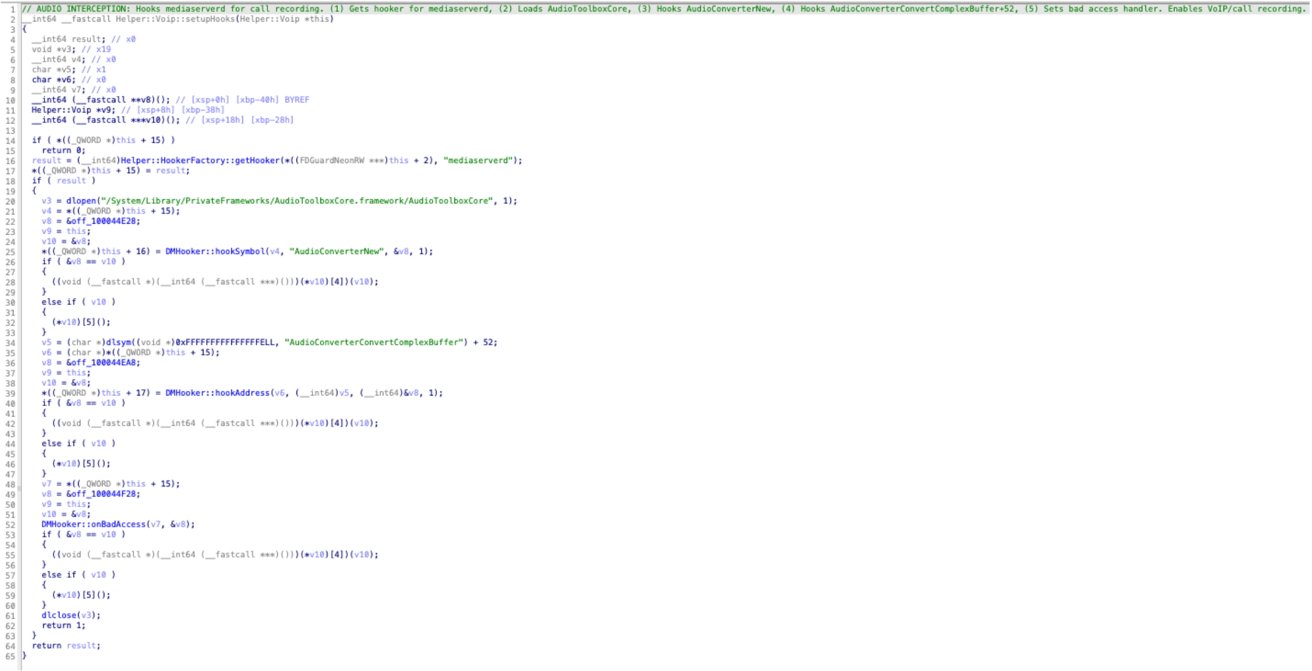
Voip::setupHooks() hooking AudioConverterNew and AudioConverterConvertComplexBuffer+52 — no indicator suppression code present. Image credit: Jamf
Next, restarting your iPhone regularly can disrupt certain post-exploitation frameworks that rely on persistence in memory. Although a reboot isn't a guaranteed fix, it can temporarily break some spyware footholds.
Keep an eye out for strange things happening with your device, like crashes you can't explain, changes to your configuration profiles, unknown VPNs, or new enrollments in device management. Advanced spyware might be sneaky and hide its signs, but it often leaves behind subtle clues.
If you think you might be at higher risk, it's a smart move to enable Lockdown Mode. This mode tightens up security by limiting things like message attachments, web technologies, and wired connections, making it much tougher for attackers to exploit your device.
Most importantly, understand the threat model. Predator doesn't bypass iOS privacy protections under normal conditions. It operates after deep compromise, meaning the most effective defense is preventing exploitation in the first place.