A sophisticated iPhone hacking technique and surveillance campaign ran rampant internationally for months, prior to a patch in iOS 26.3.
A new and severe attack vector focused on iPhones paired two different vulnerabilities into one. The "DarkSword" attack started with malicious web content in Safari, and ended with full kernel control, allowing attackers to break out of browser protections and access core parts of the system.
With that level of access, attackers can read messages and stored data, track location, access photos and files, and potentially activate the microphone or camera. In practice, it gives near-complete visibility into the device and the user's activity.
A chain like this generally takes significant resources and usually signals a targeted, high-cost capability rather than casual cybercrime. However, its reuse across different groups shows how quickly a working iPhone exploit can spread once it's built, starts circulating, and is refined along the way.
Separate campaigns reused the same core technique at the least inside Saudi Arabia, Turkey, Malaysia, and Ukraine. It's not clear how much DarkSword spread outside these nations, but the hosts of the malware focused on these four countries — initially.
Apple already patched the underlying flaws in several iOS releases by February 11, 2026.
DarkSword did not stay exclusive for long
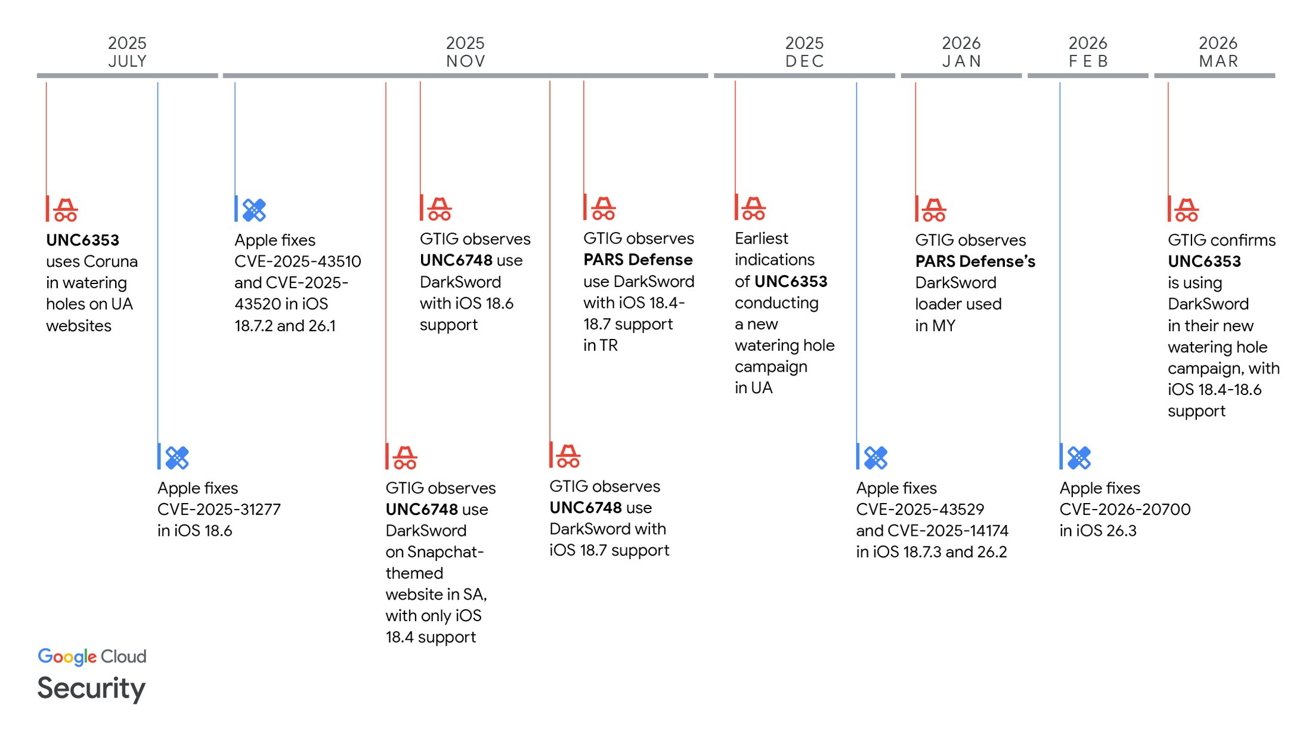
The iPhone exploit appears to have started with one group before spreading to others. It then moved quickly between campaigns, with each group using its own infrastructure and delivery methods.
Despite those differences, they relied on the same core exploitation path and underlying malware. Researchers traced DarkSword activity back to at least November 2025 and linked it to multiple campaigns.
In Saudi Arabia, attackers used a Snapchat-themed lure to trick users into visiting a malicious site. In Turkey and Malaysia, activity tied to PARS Defense shows the same technique adapted for different targets.
In Ukraine, attackers compromised legitimate websites so visitors could be infected without taking any unusual action.
These examples show how the same exploit was repackaged and deployed in different ways depending on the target.
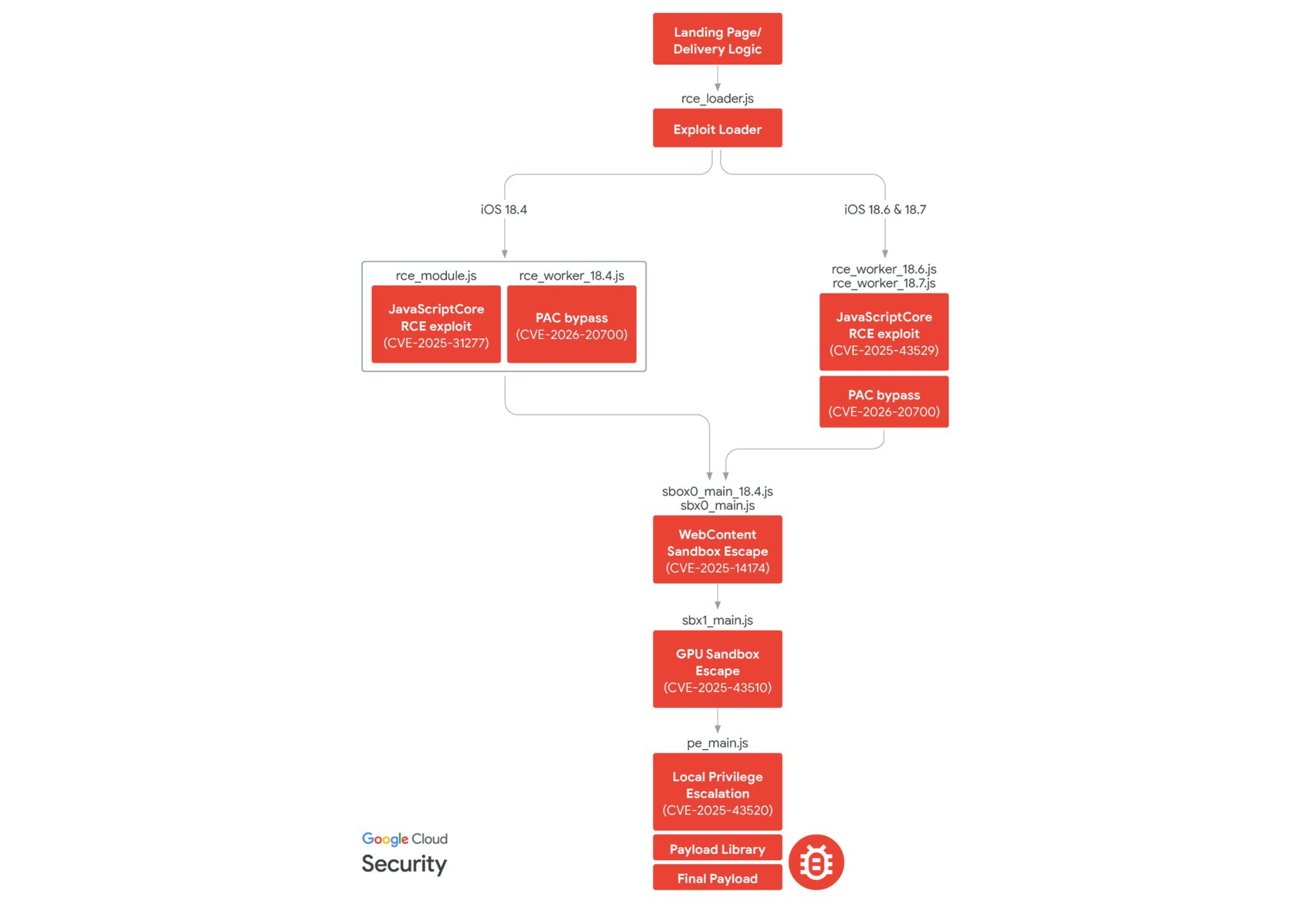
The exploit targeted iOS 18.4 through iOS 18.7 and used six flaws across several core system components. The flaws include JavaScriptCore, which handles web content, dyld, which loads system libraries, ANGLE, a graphics translation layer, and the kernel at the core of iOS.
DarkSword started in Safari and WebKit to gain initial code execution. It then escaped multiple sandbox layers before reaching full device compromise.
Some delivery logic looked basic and, in places, sloppy. One implementation loaded the wrong worker regardless of device version, while another used logic that didn't fully account for supported releases.
Those mistakes reveal how DarkSword was used in practice. The exploit chain itself was advanced enough to matter, but the surrounding wrappers were not always polished.
Apple had already patched the pieces, but the timeline still matters
Apple fixed the vulnerabilities in stages before Google published its report on March 18. Because the exploit depended on chaining multiple bugs, patching individual flaws would have broken parts of the attack before the entire chain was fully closed.
Apple's security notes for iOS 26.3 say the dyld vulnerability may have been used in highly targeted attacks.
Fully updated devices are no longer exposed to the chain, which is the key point. The timeline still matters because it shows how long an exploit can remain active before it is fully identified and addressed.
Google says it saw DarkSword activity as far back as November 2025, and one Ukrainian campaign stayed active through March 2026.
DarkSword reinforces a familiar problem for Apple
Security updates stop specific exploits, but they don't stop the commercial and state-linked market that keeps trying to build the next one. Apple's security teams are constantly defending against new attacks.
Apple can point to its fast patch cycle and say it limited the damage once the bugs were known, and the record supports that. Google's report still challenges the idea that advanced iPhone exploits stay rare just because they are difficult to build.
Once a working exploit exists, it can move quickly between operators. DarkSword fits a broader pattern where these attacks are reused across campaigns before they are widely understood.
How to protect your iPhone
Keeping your iPhone updated is the most important step. Apple fixed the vulnerabilities used in these attacks, so installing the latest iOS version closes the known paths.
Next, avoid tapping unexpected links, especially in messages that mimic apps or services you recognize. Many attacks begin by pushing users to a malicious webpage.
Stick to trusted websites and be cautious with unfamiliar ones. Some campaigns used compromised sites to deliver the exploit without obvious warning signs.
Restarting your iPhone regularly can help disrupt certain types of spyware that rely on staying active in memory.
If you think your device might've been targeted, you should consider resetting it and restoring from a clean backup. Alternatively, you could update and erase it completely to get rid of any persistent access.