Officials with the U.S. Drug Enforcement Administration are reportedly frustrated that they cannot crack Apple's iMessage encryption to listen in on suspects.
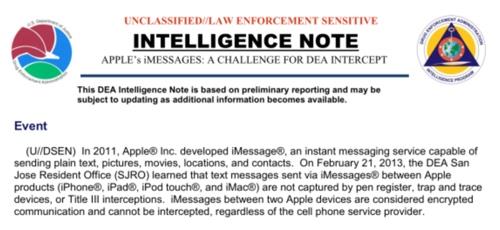
Apple's apparent stymying of the DEA was revealed in a government intelligence note obtained by CNet, which calls it "impossible" to intercept iMessages, even with a warrant. The note is entitled "Apple's iMessages: A Challenge for DEA Intercept."
The DEA is apparently only stopped if the message is an iMessage encrypted by Apple. If the message is instead sent as a text message, it's easier for the agency to obtain, though the DEA did admit that it "seems to be more successful if the intercept is placed on the non-Apple device."
The security of Apple's iOS platform vs. competing mobile operating systems like Google Android is frequently touted as a key advantage for the iPhone. The FBI's Internet Crime Complaint Center even issued a warning to users last year regarding malware that targets Android devices.
iMessages are encrypted messages that can be sent between Apple devices, including iPhones, iPads and even Macs running the OS X platform. The service launched with iOS 5 in 2011, and Apple publicly revealed that all sent and received iMessages would be securely encrypted.
DEA officials first discovered that iMessages could be a hinderance to their efforts when a real-time electronic surveillance under the Federal Wiretap Act failed to yield all of a target's text messages. The agency then discovered that the person was using iMessage, which bypassed the text messaging services of carrier Verizon.
Apple revealed in January that it sees 2 billion iMessages sent each day from a half-billion iOS devices, plus Mac computers, which gained iMessage support last year. iMessage accounts allow users to send and receive their secure messages across all their Apple devices.