A new form of iOS malware, nicknamed "AceDeceiver," can infect people without relying on an enterprise certificate or attacking jailbroken devices, security firm Palo Alto Networks revealed on Wednesday.
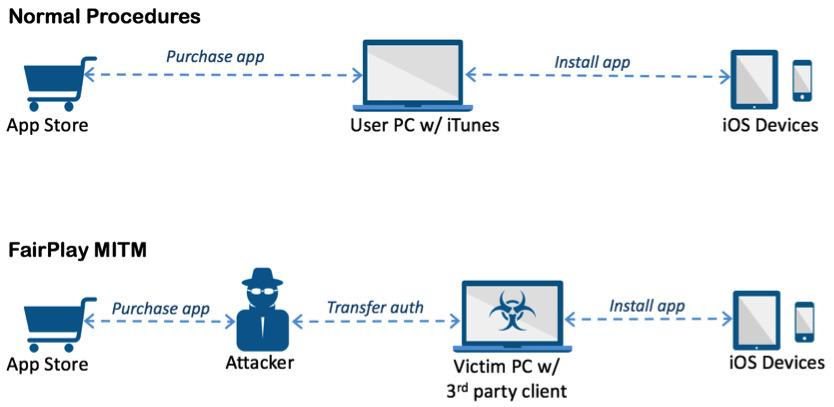
Instead the malware exploits flaws in Apple's FairPlay digital rights management, Palo Alto noted. Those vulnerabilities have used since 2013 to pirate iOS apps, but have only recently been turned to spread malware.
When fetching an app from Apple, a device normally pings the company's servers for a code proving it was purchased by a user. By intercepting such codes and crafting Windows software simulating iTunes' behavior, a hacker has been able to trick iOS devices into believing apps were bought by victims. The Windows software, dubbed "Aisi Helper," is disguised as a helpful tool but will install malicious iOS apps without alerting targets.
Three AceDeceiver apps disguised as wallpaper tools made their way onto the App Store between July 2015 and February 2016, Palo Alto said. The titles passed Apple code review "at least" seven times, the firm added, and were only removed once they were reported by Palo Alto late last month.
The apps are still a threat so long as they're installed, but are currently set to be malicious only in mainland China. Running them connects to a third-party app store where people are encouraged to enter their Apple IDs, which are then stolen and uploaded to a server.
Apple normally prides itself on iOS' security, but has still had to periodically remove App Store titles because of dangerous code. In November, for instance, the company pulled an Instagram client called InstaAgent after it was discovered collecting usernames and passwords.